Process-Aware,
OT Native
Cybersecurity
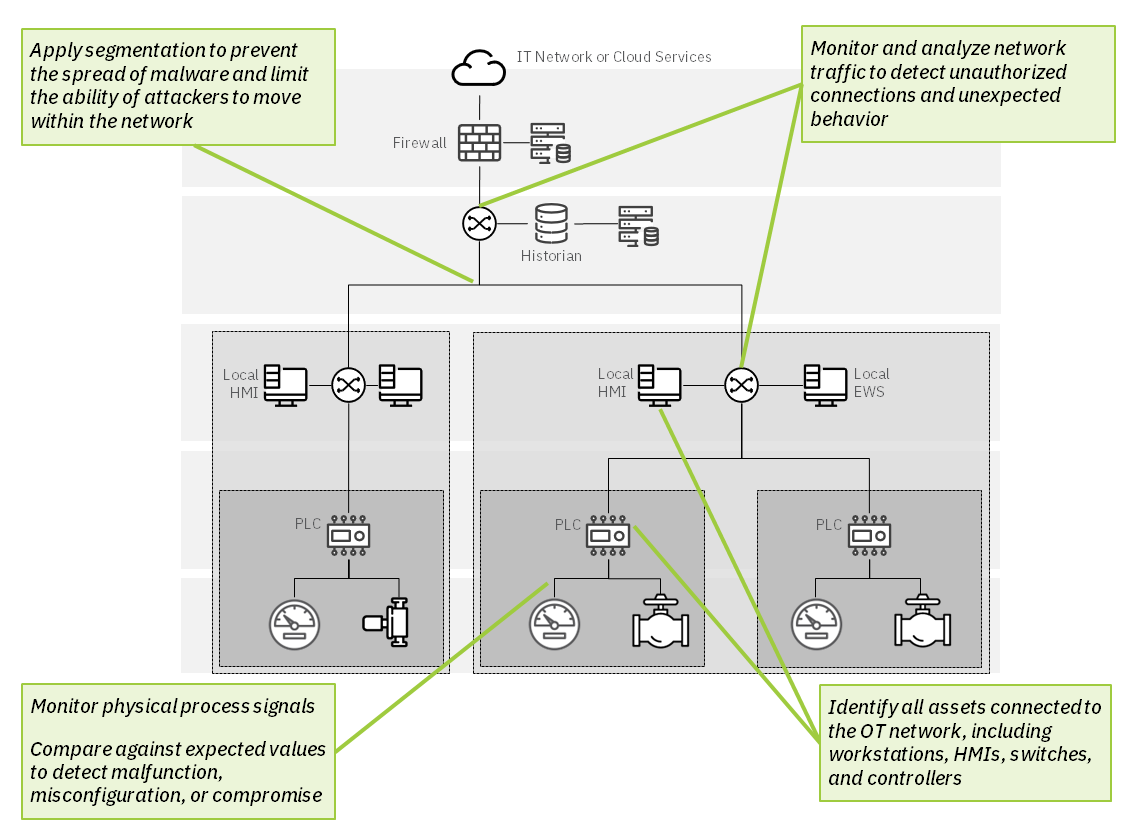
Effective industrial security requires a solution that understands your industrial process, all the way down to Level 0.
Mission Secure helps critical infrastructure operators minimize risk and prepare for tomorrow's cyber threats.
Mission Secure: 3-Minute Demo
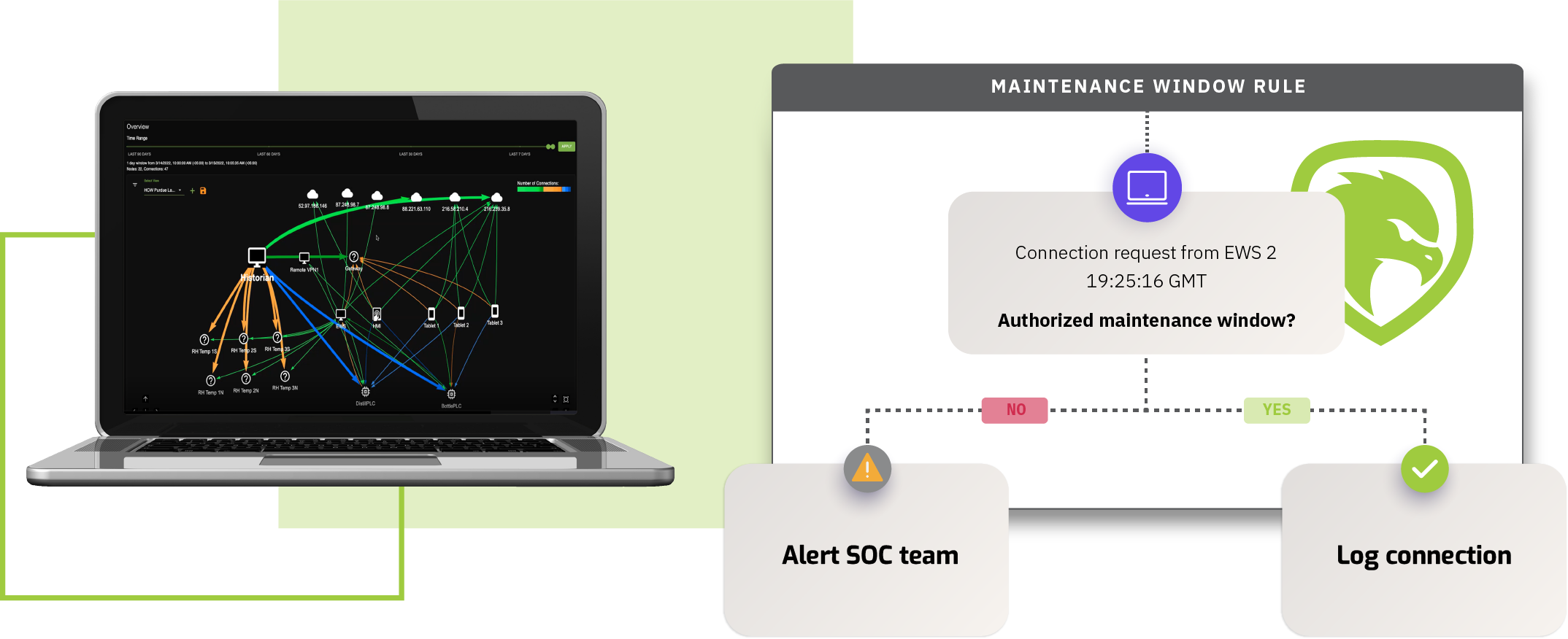
Mission Secure's OT cybersecurity platform delivers industry-leading asset inventory, vulnerability management, and anomaly detection capabilities. Check out this short video for glimpse of what Mission Secure has to offer.
For a full demonstration of the Mission Secure platform and to learn more about how we can help you identify and mitigate OT cyber risk, contact us today!
OT Cybersecurity News and Updates
-
Blog
Protecting Shipboard OT Systems
A look at how Mission Secure is helping maritime owners and operators protect their assets in a rapidly evolving environment. Read More » -
Industrial Cyber
Growing Need to Safeguard Industrial Systems
Mission Secure shares insights with Industrial Cyber on the fundamental strategies and technologies needed for an effective OT cybersecurity program.
Read More » -
Blog
Beyond Cybersecurity: How an OT Asset Inventory Can Boost Operational Efficiency
A detailed, up-to-date asset inventory is essential for identifying and prioritizing software vulnerabilities, misconfigurations, and other cyber risk factors. But that’s not all an OT asset inventory can do Read More » -
S4x23
Automatic Recovery at Level 0
Mission Secure's Jens Meggers on stage at S4x23, describing an innovative approach for automated response and recovery when attacks target the lowest levels of an ICS network. Read More »
Create and deploy fine-grained OT cybersecurity policies with Mission Secure's proven technology
Industry-Specific Solutions
Mission Secure's OT security solutions are purpose-built to meet the unique needs of critical infrastructure assets and networks.
-
Oil & Gas
Read More » -
Maritime
Read More » -
Power
Read More » -
Smart Cities
Read More »