Protect Your Manufacturing Industrial Control Systems
Internal and external security threats can lead to revenue loss and operational disruptions — keep your facility up and running with Mission Secure.
Improve your security profile and manage cyber operational risks
Mission Secure maintains real-time visibility and protection to make sure every machine and every device on your network is locked down against cyber threats.
Guard your facility against revenue loss by limiting production distractions and better protecting your ICS network.
Manufacturing markets we serve:
- Food and Beverage
- Pharmaceuticals
- Chemicals
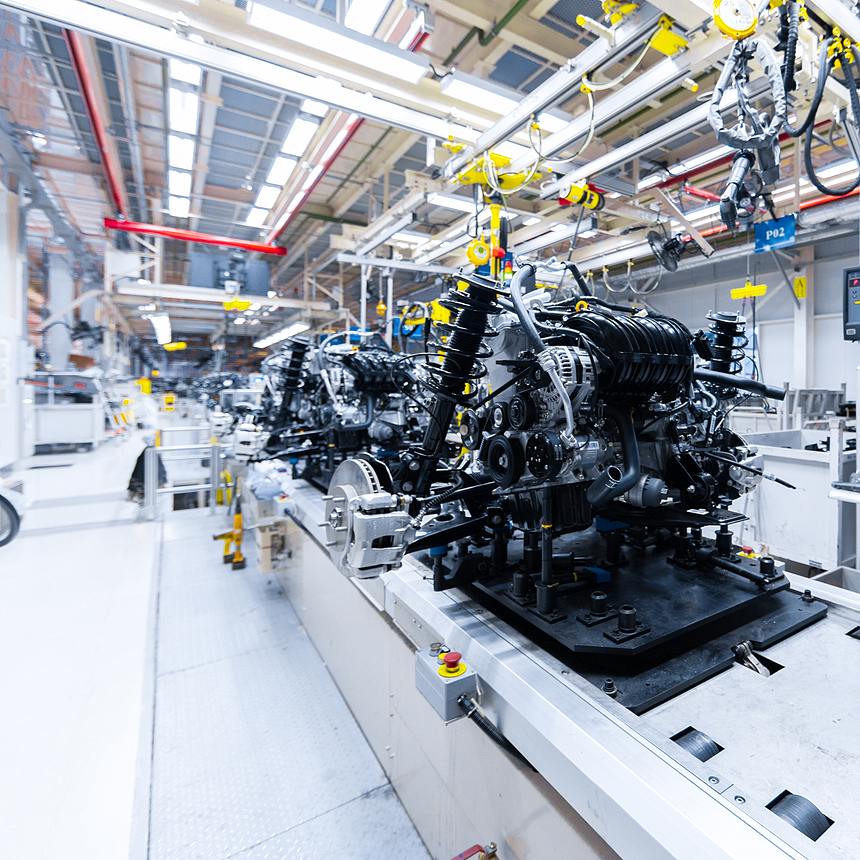
- Automotive
- Appliances
- Other Critical Manufacturing Sectors
Helping you meet your OT cybersecurity goals
Since 2014, Mission Secure has delivered advanced, OT native cybersecurity solutions to help critical infrastructure operations stay safe, reliable, and productive.
-
Equipment monitoring
Real-time monitoring to verify equipment is running to specification. -
Network segmentation
Implement a zero trust defense to protect your critical infrastructure using network zone segmentation. -
Access control
Control of any third party accessing your network and limit specific access according to need and use. -
CISA & NIST compliance
Assess your current compliance with key components of the regulatory frameworks and address gaps to protect your facilities.
Demonstrate compliance with key governmental and industry standards
Along with protecting against OT cybersecurity threats, our industry experts help manufacturing clients address regulatory compliance — including the CISA and NIST requirements. Successfully navigate through compliance regulations with Mission Secure.
Compliance standards we support:
- NIST
- NIS2
- ISA/IEC 62443
- ISO/IEC 27001

Signal integrity monitoring for key production assets
Maintain reliability and productivity, and ensure no internal or external malicious actor tampers with production assets without detection.

The Mission Secure Platform
Mission Secure delivers the only OT cybersecurity platform that enables complete control over your environment, including visibility, anomaly and threat detection, policy enforcement, and Level 0 signal validation.
-
Asset and Network Visibility
Discover and visualize every asset and every network connection in your OT environment
Learn More » -
Anomaly and Threat Detection
Identify unexpected or unauthorized activity, from Level 0 signals to cloud connections
Learn More » -
Policy Enforcement
Segment your network and enforce granular policies for true Zero Trust cybersecurity
Learn More » -
Signal Integrity Validation
Monitor physical process signals to detect threats and prevent system damage
Learn More »

Case Study
Gain clear OT network visibility
This North American-based Pulp and Paper Mill partnered with Mission Secure for a cybersecurity assessment to understand the full extent of their security vulnerabilities.
Doing so helped them to build a security program tailored to their OT environment, minimizing network downtime and improving cybersecurity protection of their critical production facilities.
Serious risks to our operational uptime cannot go unaddressed – whether physical, safety or cyber risks. Working with Mission Secure to maintain visibility and protection of our plant control system network gives us greater confidence in the resilience of our operational systems.” - Manufacturing, Senior Director of ITRead the Case Study
Protect your OT network
Mission Secure delivers the technology and expertise you need to begin your journey toward Zero Trust, and to implement intelligent, resilient cybersecurity in your OT network, while enhancing—not disrupting—reliability and productivity.
Get in contact to schedule a consultation with our OT cybersecurity experts today!
Resources
-
Case Study
Improved Cybersecurity Helps Paper Mill Manufacturer Extend Control System Lifespan
Read More » -
Guide
A Comprehensive Guide to Manufacturing Cyber Security
Read More » -
Blog
Cyber Threats to the Manufacturing Industry
Read More »