5 Min Read
The OT Cybersecurity Blind Spot: The need for visibility and protection for Level 0
Written by Ed Suhler
From the notorious Mærsk NotPetya cyber incident to the Ryuk attack affecting port operational control systems, the increasing frequency of successful operational technology (OT) cyber attacks serves as a wakeup call to all network administrators, IT and OT alike: the smallest hole in today’s cyber defenses gives adversaries a vector for attack.
Cyber attacks: increasing frequency and escalating sophistication
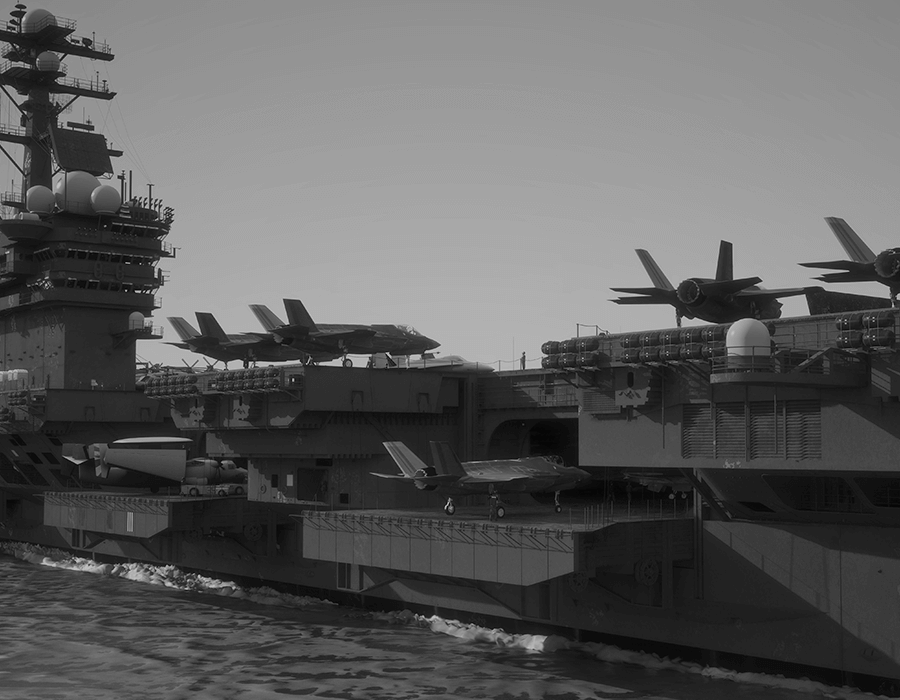
This revelation should be especially alarming to OT system operators in the critical defense infrastructure space across the U.S. military branches, on whom the country relies for successful mission execution. One cannot “patch” their way out of this problem. A determined adversary with the resources of a nation-state will penetrate even the best perimeter defenses.
To make matters worse, now a proliferation of tools and malware are readily available to adversaries or bad actors, enabling them to launch attacks without significant resources. The bottom line? Someone who is determined and talented will find a way in.
The OT cybersecurity blind spot: a call for cyber resiliency
The escalating attack frequency, combined with an increasingly sophisticated threat landscape, highlights the need to make critical systems more resilient to cyber threats. Organizations and governments must deal with scenarios where they are actively under a cyber attack, requiring a proactive response, not just a reactive one. A cyber attacker has found their way into their networks and systems, now what?
There is a clear need to build methods to monitor and detect cyber threats at more granular levels, thus pushing the cyber protections out to where the impact happens—the cyber-physical processes within the mission-critical OT environment.
A “bottoms up” approach to OT cybersecurity
To address the OT cybersecurity blind spot, take a “bottoms up” approach, and protect the mission-critical cyber-physical processes within the OT environment. Put cyber protections in the physical processes on which mission execution relies—navigation; propulsion; hull, mechanical and electrical (HM&E); combat and weapons; and aviation controls. This approach is a fundamental paradigm shift, focusing protections at Purdue Reference Model Levels 0, 1, and up in addition to perimeter protection and firewalls at the higher, IT-oriented Levels.
Using comparative analysis and change detection between the digital and raw physical signals with system awareness provided at the network traffic level, a “bottoms up” approach provides operators unprecedented insight and protection from the individual component level (Level 0) throughout the ICS ecosystem to the network traffic layer (Level 3).
This method should include monitoring and protection capabilities spanning both the entire IT network as well as the control systems that sit on those networks and control the physical processes. And thus, naturally, the “bottoms up” approach complements more traditional IT approaches prescribing barriers to limit the attack surface and prevent adversaries from entering.
Similar to a missile warning system (MWS) on a tactical aircraft, this approach can continuously monitor for cyber threats—even zero-day attacks, compromised supply chain components, or an active attack. The “bottoms up” approach to cybersecurity changes the game for control system resiliency, defense-in-depth, and the ability to maintain positive control over critical systems and processes requiring the highest levels of protection.
Addressing resiliency in the OT environment
Now, where does one start in a “bottoms up” approach? How do operations address the cybersecurity requirements of the OT environment? The logical first step is to audit the current cybersecurity posture for control systems. Where is your organization today? Where are the security gaps, and what actions are best to mitigate those risks?
A warning: Audits or cyber assessments typically adopt a compliance-based approach when looking at cybersecurity. Compliance is not security – although it is often treated that way.
Most organizations begin with an assessment as a place to start their journey towards defense-in-depth security for operational technology systems, such as those found in across defense infrastructure. However, this is only a place to start. Establishing cyber protections down into the lowest part of the OT infrastructure requires a comprehensive assessment, across IT and OT, and thorough cybersecurity design.
Bringing IT and OT together
A common pitfall, but a critical part of the OT cybersecurity process is getting the operations and IT departments to work together to address the gaps identified in the cybersecurity assessment. Often IT professionals do not know how OT systems operate, the protocols and processes used, and the potential impacts security recommendations for control systems could have on operational processes or the business as a whole. The same is true for operations people; they often do not have the in-depth cybersecurity capabilities of a trained IT professional. The trick is to bring the two groups together to find people, process, and technological solutions that will protect the OT environment without disabling the defense and mission-critical capabilities we are trying to protect in the first place.
Making the control systems resilient to threats with the ability to isolate or prevent potential operational impacts is the goal. This level of resiliency requires new layers of technologies focused on assuring mission success, including better monitoring, detection, and forensics at Level 0. But control system resiliency also requires new protections built for the protocols and processes found in the OT environment as well as the ability to provide corrective capabilities to ensure mission completion and success. This level of OT cybersecurity is far more than just firewalls; it is a new approach requiring a new breed of software and hardware tools built specifically for the OT world. Without a new approach, addressing the risks and protecting OT systems without impacting operational performance will remain a challenge for years to come.
Steps towards OT cyber resiliency
Whether we look at building control systems, HVAC, power generation and distribution, fuel depots, base security, or the weapons system platforms themselves—autonomous vehicles, ships, air vehicles, ground vehicles, among others—they all share control systems that were built for efficiency and reliability but typically not for cybersecurity. This reality is even direr for environments with legacy equipment.
OT systems will not be replaced wholesale with more secure systems any time soon. And they need to be cyber resilient, encompassing capabilities for monitoring, detection, correction and protection, today. It is no longer enough just to keep the adversary at bay. A new approach is needed to ensure that critical operational functions continue in the face of a cyber threat.
Attacks to OT systems risk long-standing shutdowns for industrial operations or make them unreliable in air, sea and land operations. Lives and mission success are at stake. While there is a natural tension around defense funding, resources, and allocation—whether one allocates resources to cybersecurity versus addressing additional mission-critical operational needs—let’s face it, cybersecurity is an insurance policy. Now, however, the ramifications of not addressing the cyber resiliency in the field for OT systems are working with unreliable weapons platforms that may not operate as designed during mission execution.
As more of our critical logistical support systems, mission operational systems, and critical communications systems become even more automated, the risks associated with cyber threats are magnified in the field. It’s time to address the blind spots now and make critical control systems and OT networks cyber resilient. OT security now is part of the insurance policy.
About Ed Suhler
A co-founder of Mission Secure, Ed currently serves as the Vice President of OT Cybersecurity Implementation Services, where he focuses on implementing Mission Secure’s patented technology to secure client operations from cyber risks. Ed often leads as the technical project manager for customer engagements, including Fortune 10 and 1000 clients in oil and gas, maritime, smart cities, and defense industries. Ed cybersecurity projects cover a range of control systems and critical assets, including transportation management systems, power distribution systems, and unmanned aerial systems (UAS) for the U.S. Navy.
Ed holds five patents for applications of cyber protections to cyber-physical systems and has filed additional patents on his research efforts on system-aware cybersecurity methods and techniques. He’s authored numerous white papers on the application of system-aware cybersecurity and its use in industries such as transportation, oil and gas, autonomous systems, and electrical distribution systems. Ed holds a Bachelor of Science in Management and Management Information Systems from the University of Virginia.
Originally published February 11, 2020, updated November 19, 2020.


