24/7 OT Cybersecurity Support with Mission Secure Managed Services
IT and OT expertise to manage your cybersecurity program or augment your existing team to stop OT cyber threats head-on.
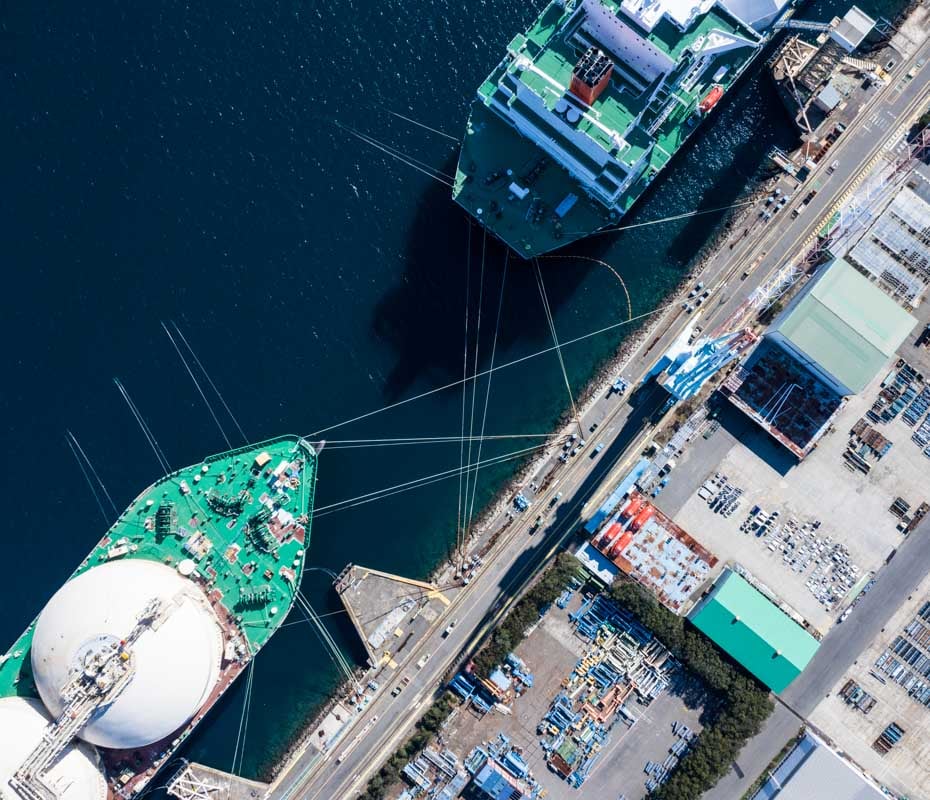
Monitoring the health status of all devices in your OT network as your eye in the sky.
As an add on to the Mission Secure Platform, our managed services team ensures your operational technology (OT) and ICS networks are locked down no matter where you stand in your OT security program.
-
Skills and Expertise
With a wealth of OT and IT cybersecurity expertise, our team is positioned to support as needed, whether on a consultative basis or taking a primary role in keeping your OT networks secure. -
Technology and Tools
Mission Secure's managed services team uses our state-of-the-art technology and tools to enable real-time response and support. Our platform enables advanced OT threat and anomaly detection, while minimizing false positives and disruption. -
Methodology and Approach
Every Mission Secure solution has been put to the test, and all of our devices are utilized and trusted by our own team. You can rest assured that the devices you use, the managed services team you trust, have all been well trained and tested. -
Certifications
Mission Secure’s managed services team brings together experts from ICS, OT, IT, cybersecurity, and ethical hackers. Certifications include:
- Certified Information Systems Security Professional (CISSP)
- GIAC Cyber Threat Intelligence (GCTI)
- Certified Cloud Security Professional (CSSP)
- Certified Ethical Hacker (CEH)
- And many more
Managed Visibility For All Assets
Improve your ability to withstand OT cyber threats with a named security engineer and certified team. Have the support you need at every turn.
- Accurate visibility graph
- Asset customization and labeling
- Continuous OT asset and communication monitoring
Proactive Managed Protection
Knowing what to block starts with 24/7 continuous remote OT coverage that protects against intrusion and weakness.
- Analysis of your current network
- Critical insight on traffic patterns
- Baseline data for existing traffic profiles
- Implement and maintain best practice protections
- Mitigating controls for unpatched vulnerabilities

Managed Analysis and Hunting
We’re proactively looking out for your OT network and bringing you accurate information before there’s an issue to eliminate threats.
- On-going network assessments and analysis
- Threat and vulnerability hunting
- Vulnerability protection recommendations
- Comprehensive reporting to keep you informed

Managed Response and Support
Our team of cybersecurity, threat intelligence, and digital forensics experts are experienced in helping organizations face the threat of cybersecurity incidents.
- Immediate investigation into suspicious activity
- Reliable 24/7 support
- Security incident response to eliminate and recover from threats

Additional Managed Services Features & Benefits
-
Named security engineer
-
Ongoing OT network analysis
-
Threat detection and hunting
-
Redundant and secure backend
-
Security information and event management
-
Secured end-to-end
Especially in the OT environment, cybersecurity resources and expertise are scarce, and it impacts our clients around the world. With Mission Secure Managed Services, we take on this burden, supporting our clients every step of their journey — making the path to OT cyber-protection easier and financially feasible."
Don Ward, SVP Global Services, Mission Secure
Having the Mission Secure solution protecting our traffic signal system network backed by a very flexible and responsive support team before and during our deployment has been crucial for us, and we’re looking forward to a continued relationship."
Chief Traffic Management Engineer
Resources
-
Guide
A Comprehensive Guide to Operational Technology (OT) Cybersecurity
Read More » -
Datasheet
Mission Secure Managed Services
Read More »