3 Min Read
Australia Targeted: Confronting a Nation-state Cyber Attack
Written by Mission Secure

On June 18, 2020, the Australian government's Cyber Security Centre issued Advisory 2020-008 regarding the "sustained targeting of Australian governments and companies by a sophisticated state-based actor." According to multiple reports, institutions such as hospitals and state-owned utilities have been under attack for months.
In a notably rare occurrence, Australian Prime Minister Scott Morrison publicly acknowledge being under an ongoing state-sponsored cyber-attack. Morrison called for the public to be aware and warned during a live briefing, stating:
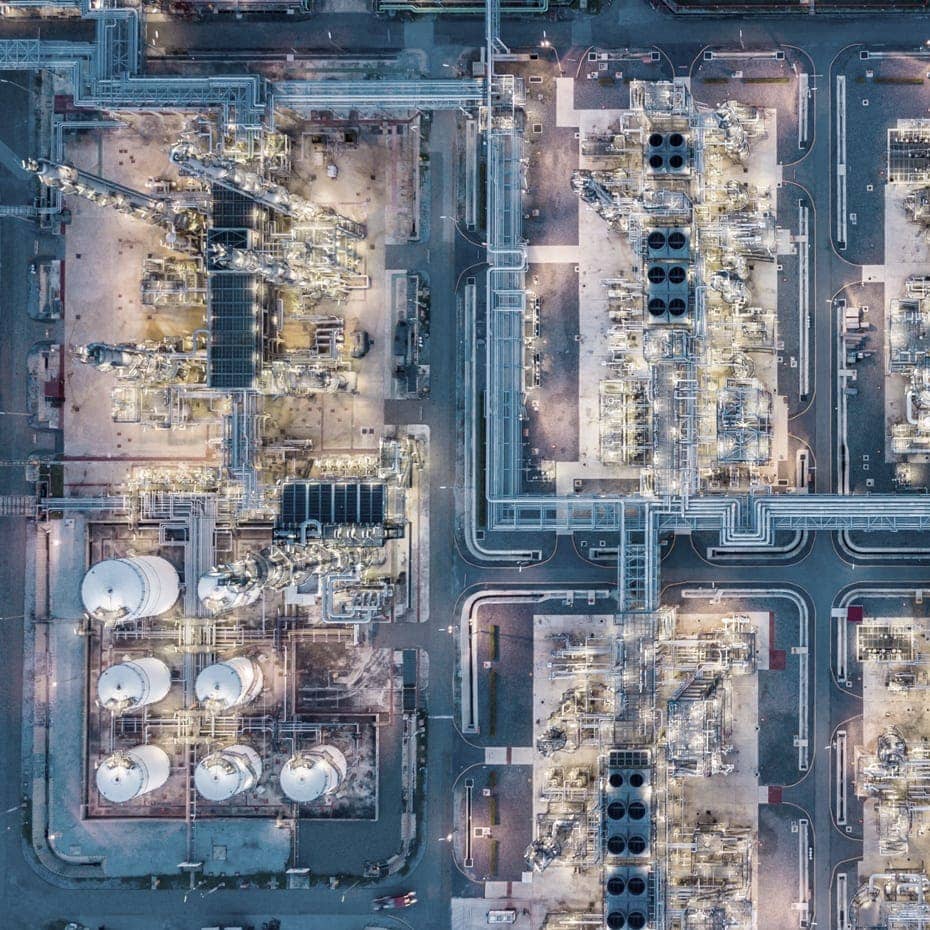
"This activity is targeting Australian organizations across a range of sectors, including all levels of government, industry, political organizations, education, health, essential service providers, and operators of other critical infrastructure."
"It's stunning to see a Head of State admit to a sophisticated months-long cyber-attack across the breadth of industries, government institutions, and public service organizations," comments Ed "Otto" Pernotto, Mission Secure's co-founder and Senior Military Advisor.
While the suspected nation-state wasn't named by the Australian government, cybersecurity experts largely believe China is behind the spread of cyber-attacks. According to the Financial Times, Tom Uren, cybersecurity analyst at the Australian Strategic Policy Institute, stated, "Of course it is China. There are a few countries that have the capability: Russia, China, US, UK, and perhaps Iran and North Korea, although they may not have the scale. Only China in this list will have the appetite for such a broad approach." Various reports and comments from cybersecurity experts reinforce the likelihood that China is behind the cyber-attacks. A claim that has been denied by the Chinese Ministry of State Security.
Retaliations in Cyber Space
As BBC reports, the timing of the cyber-attacks also seems to reinforce China as the culprit behind the attacks. Australia recently called for investigations into the origins of COVID-19. In response, China imposed tariffs and discouraged its citizens from traveling to Australia.
Australia also banned the Chinese technology giant, Huawei, from participating in its national 5G infrastructure work due to national security concerns, another point of contention between the two nations. The basis of the ban is Chinese law, which requires "organizations and citizens to support, assist, and cooperate with intelligence work"—a law some analysts say make Huawei a "conduit for espionage." Former Australian officials cite the increasing cyber-attacks over the last months as retaliation for the ban.
A String of Cyber-attacks
Neither Morrison nor the advisory went into detail on the cyber-attacks. However, there have been a string of high-profile attacks in the headlines spanning industries and at varying levels of severity. As previously shared by Mission Secure, 2020 attacks impacting physical operations or operational technology (OT) include:
BlueScope Steel (Mining & Metals): The "third largest manufacturer of painted and coated steel products globally" suffered a cyber incident in mid-May, causing some production and manufacturing operations to halt, including production at its Port Kembla site.
Lion (Food & Beverage): Sydney-headquartered beverage giant suffered two cyber-attacks over the last weeks, causing production to stop and creating a supply shortage. The Lion cyber-attack is currently believed to be Russian-based. However, coincidentally, Lion is also "the subject of a $600 million takeover bid by foreign business China Mengniu Dairy." Also noteworthy, Mengniu is partially owned by a Chinese state-owned food processor, COFCO.
In addition to cyber-attacks physically impacting commercial production activities, the Australian logistics giant, Toll Group, suffered two ransomware attacks over three months, causing customer delays and business disruptions. Defense manufacturers, government contractors, and accounting firms also reported data breaches previously.
A Call for Cyber Resiliency
The requirement for a robust cybersecurity program in today's digital age is not new news. But the increasing frequency, sophistication, and scale of cyber-attacks, as seen in Australia, is a call that cybersecurity must be the first thought in adopting and deploying technology—instead of an afterthought. "This may represent the ratcheting up of conflict without any apparent loss of life or damage to actual systems," states Pernotto. "However, it further demonstrates the need for continually improved defensive capabilities that are flexible, robust, and extended across both information technology and operational technologies."
Operational technology and industrial control systems need to be protected to make today's critical infrastructure cyber-resilient. Yet, OT cybersecurity lags IT cybersecurity by years. Ed Suhler, Vice President of Implementation Services and U.S. Department of Defense Projects at Mission Secure, has previously written and spoken about the OT cybersecurity blind spot, publishing earlier this year:
"The escalating attack frequency, combined with an increasingly sophisticated threat landscape, highlights the need to make critical systems more resilient to cyber threats. Organizations and governments must deal with scenarios where they are actively under a cyber attack, requiring a proactive response, not just a reactive one. A cyber attacker has found their way into their networks and systems, now what?
There is a clear need to build methods to monitor and detect cyber threats at more granular levels, thus pushing the cyber protections out to where the impact happens—the cyber-physical processes within the mission-critical OT environment."
Across industries—power generation and distribution, metals and mining, pharmaceutical, or food and beverage—they all share control systems built for reliability and productivity, but not cybersecurity. As Suhler states, "It's time to address the blind spots now and make critical control systems and OT networks cyber resilient." It's required to combat cyber adversary, from wherever they may come.
Originally published June 22, 2020, updated May 24, 2023.