4 Min Read
Defense in a Cyber-Physical Era: Escalating cyber attacks and inadequate protections
Written by David Dresher

The next era of geopolitical warfare has arrived. What now? It’s a question posed merely a month ago. Since then, its importance and impact have broadened over the ensuing weeks.
Following cyber attacks on critical infrastructure and government assets in Bahrain, the Wall Street Journal reports increasing “…fears among leaders in the region that Tehran is stepping up its cyberattacks….” Iranian geopolitical tensions continue to rise across nations. (ICYMI: Timeline of Recent Events.) With kinetic and non-kinetic actions taking place in the Persian Gulf, retaliation against U.S. government and critical infrastructure, and recent events illuminating this new era of warfare, cyber attacks on physical assets are becoming more frequent. They are the new norm. The question remains: what now?
The Case of Stena Impero
In an “extraordinarily brazen” move according to CNBC, Iran seized British-flagged tanker, Stena Impero, in mid-July citing maritime violations. The 2018-built Stena Impero is a Swedish-owned vessel with a crew of 23; the Impero flies a British flag meaning protection for the vessel and crew falls under the watch of the U.K. A second British-owned-and-operated tanker, the Mesdar, was also momentarily retained while Iranian armed guards boarded the vessel, only to be released with a warning. Just last week, Iran allegedly seized a third tanker.
With global trade tensions escalating, the maritime industry has increasing economic risk. Meanwhile, tens of thousands of vessels carrying crucial cargo are at risk of disruptive cyber attacks that could have operation, financial and reputational implications. These vessels require enhanced defense capabilities to protect operations.
Dissecting Cyber-Physical Vulnerabilities
As covered in TradeWinds, The Global Shipping News Source, unconfirmed reports indicate Britain’s MI6 unit is investigating whether the Stena Impero fell victim to GPS or global navigation satellite systems (GNSS) spoofing which caused the vessel to inadvertently venture into Iranian water. GPS spoofing and jamming are common attack methods the U.S. military, and its allies, have faced in Afghanistan, Syria, Iraq and more. The maritime industry has also suffered from this attack vector before.
In 2017, Maritime Executive reported a GPS-spoofing attack affected over 20 vessels in the Black Sea, causing one vessel to be 25 nautical miles off position. Upon further investigation, the vessel’s onboard control systems confirmed GPS signals were spoofed, providing false and inaccurate information. Mission Secure has been working on GPS spoofing and jamming solutions for the U.S. military since the company’s inception in 2014. Compromised GPS represents one of many potential attack vectors facing the maritime industry.
In early 2019, a commercial vessel experienced a cyber attack that “significantly degraded functionality” of the vessel’s shipboard network. In 2017, Maersk fell victim to NotPetya; according to Maersk chief information security officer (CISO) Andy Powell, “(The cyber attack) effectively took out the majority of the company’s capability in terms of IT within literally a few hours. Wired reported it took months to recover costing the company $300 million. When asked about lessons learned, Powell states, “You’ve got to be prepared.” It’s a message the U.S. Coast Guard can’t stress enough, writing:
“Maintaining effective cybersecurity is not just an IT issue, but is rather a fundamental operational imperative in the 21st century maritime environment. The Coast Guard therefore strongly encourages all vessel and facility owners and operators to conduct cybersecurity assessments to better understand the extent of their cyber vulnerabilities.”
Maritime vessels, like other critical and industrial operations, possess numerous cyber-physical attack vectors; navigation waypoints, steering and heading controls, communication systems and others are vulnerable to cyber manipulation with tangible, kinetic impacts. It’s never been more important to protect these key assets and the operations that rely on them from new cyber threats.
What Now? A Mission to Protect Maritime Vessels
As we watch these events unfold—using cyber attacks as offensive and retaliatory measures in conjunction with kinetic attacks—it’s increasingly clear maritime cybersecurity must be on par with the culture of safety. What now?
Assess Cyber Vulnerabilities and Risks: Assessing the current state of vessel cybersecurity is always the first step. Every owner and operator should start by conducting a cyber risk assessment of the OT and IT networks controlling the most important assets and platforms. The goal of the assessment is to identify the most critical OT and IT cyber risks and close any immediate gaps.
Design a Secure Cybersecurity Architecture: A robust cyber architecture will involve people, process and technology—elements required for any successful implementation. Like safety, cybersecurity must become a mantra and be embedded in your culture and operations to be effective. Also worth noting and similar to safety, a robust cybersecurity program doesn’t have to be cost-prohibitive and it must address the unique challenges of vessels at sea, such as low to no connectivity during periods, limited to no IT or networking technical support on the vessels and third-party remote access to vessel systems. Modern vessels require a combination of onboard asset discovery, network mapping, network traffic monitoring, segmentation and endpoint protection to mitigate cyber risks.
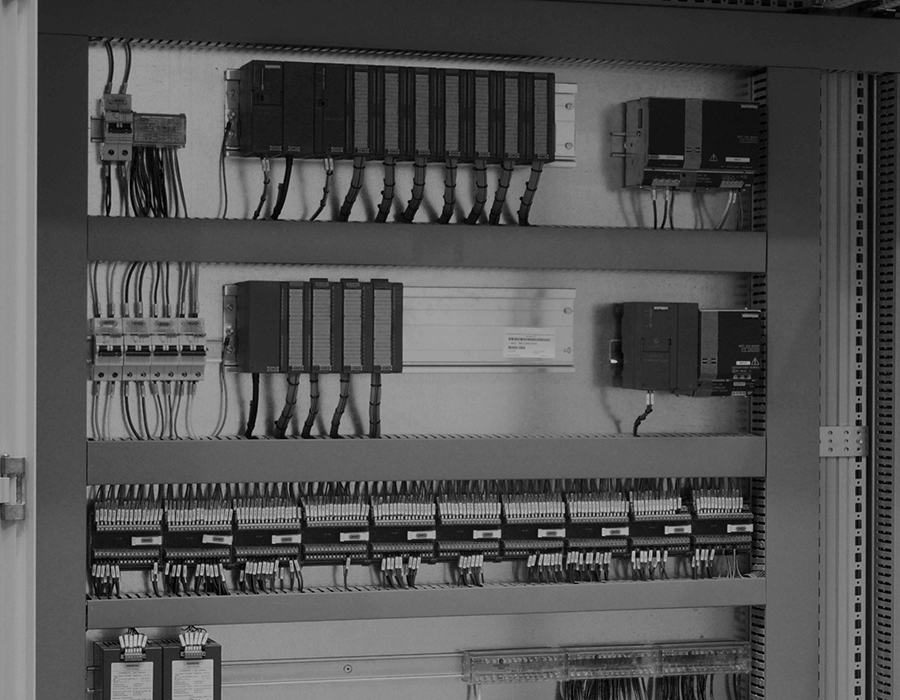
Deploy Protection and Continuously Monitor: Actual protection requires hardware to be embedded into the control network, monitoring control system activity and being able to control unwanted or abnormal actions. Most maritime organizations want a purpose-built cybersecurity solution, like the Mission Secure Platform, to provide control system network visibility, protection and ongoing monitoring down to Level 0. Network segmentation, controller and endpoint protection, encryption and additional intrusion prevention and remediation capabilities are also indispensable. A unified, on-vessel, single-window approach is typically recommended as solutions are usually implemented in a complex environment. Protect control systems and operations through implementing a secure cyber architecture and deploying cost-effective, scalable solutions encompassing people, process and technology. Monitor alerts and be proactive in follow-up and action management.
Working with a number of leading maritime companies among numerous others in energy, transportation and defense, Mission Secure is on the frontlines to protect the maritime industry from cyber threats. A recent Forbes article poignantly articulated today’s cybersecurity environment, stating, “This is the hybrid warfare we now face, cyber and physical, military and civilian, direct and indirect.” We live in a new cyber-physical era. And it’s prudent for all to not wait until it’s too late to protect operations.
Begin Your Mission, Secure Your Operations
The realm of cybersecurity for industrial and critical infrastructure continues to evolve, and as such, we must evolve with it or face the consequences. While technology and today’s digital transformations hold clear benefits, they also pose an untold number of cyber risks—risks whose impact escalates with the nature of the operations.
Ready to start securing your vessels from cyber attacks? Start with an in-depth OT and IT cybersecurity assessment of your operations facility and vessels. Contact us to learn more or meet our CTO, Dan Park, and Chief Cyber Evangelist, Weston Hecker, at the Hack The Sea village at DEF CON 27 this Sunday, August 8th.
To learn more about maritime cybersecurity, check out this case study.
Originally published August 9, 2019, updated November 19, 2020.