3 Min Read
Industrial Control Systems: The New Target of Malware
Written by Paul Robertson
During 2020, CISA issued 38 cyber alerts ranging from nation-state actors like Iran and North Korea to known ransomware specifically targeting pipeline operations and notably the last alert issued on December 17, 2020, Advanced Persistent Threat Compromise of Government Agencies, Critical Infrastructure, and Private Sector Organizations, for the SolarWinds supply chain attack.
2020 represents a 660% increase in cyber alerts over 2019, during which CISA issued five cyber warnings over the full year.
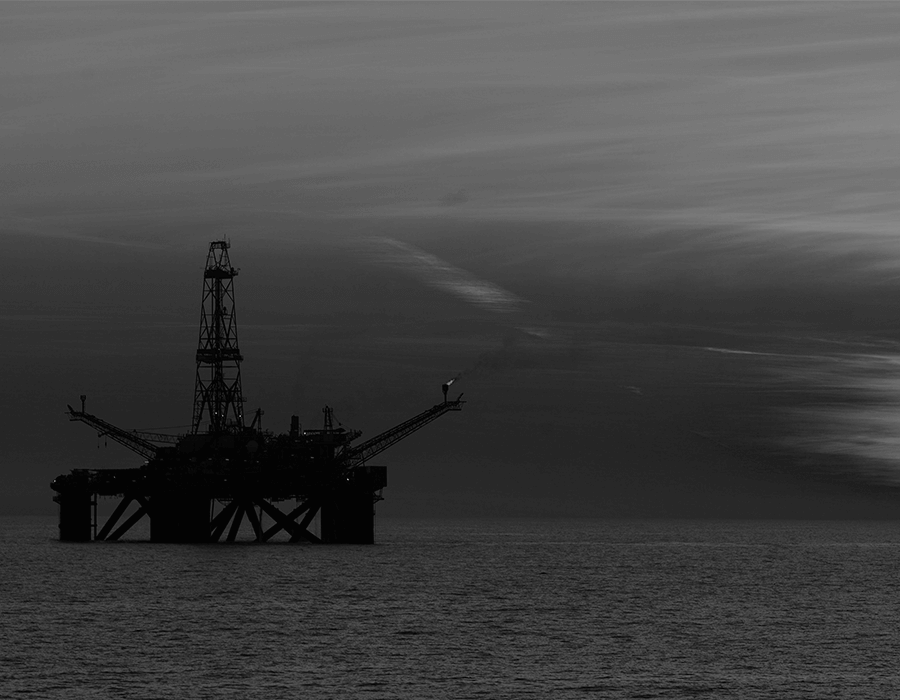
Organizations across the board also saw a growing number of adversaries targeting and attacking industrial control systems (ICS) and operational technology (OT) networks. It’s a trend that is clearly continuing into the new year (‘Dangerous Stuff’: Hackers Tried to Poison Water Supply of Florida Town).
And as the attack surface continues to expand for critical infrastructure with owners and operators adopting new technologies to improve operational efficiencies, the increased vulnerabilities and targeting of ICS systems and OT networks is expected to rise.
Targeting OT networks and the increase ICS-focused malware
On the IT side of the house, malware is a big industry. Ransomware (a type of malware that restricts access for a ransom payment), for example, is forecasted to reach $20 billion in global damage costs this year, nearly double the figure in 2019 and triple the 2018 number.
And there is clear precedent for the quick payout nature and ROI of ransomware activities. Last year, Garmin fell victim to WastedLocker and reportedly paid a $10 million ransom. Other 2020 ransomware victims include electronics manufacturer Foxconn, a U.S. pipeline, and Toll Group — who was hit twice during the year — to name a few.
There’s also been an increase in the level of programming and flexibility of malware over the last few years. And this new breed of malware has been increasingly deployed in attacks — impacting both IT and OT systems alike.
Modular malware: ICS modules housed within IT malware
Modular malware, as the name suggests, contains different modules. These modules can be dynamically loaded onto target systems within a particular environment. For example, if the victim has a Windows 7 PC, a module with Windows 7 exploits can be loaded to target that specific asset. This isn’t a new tactic.
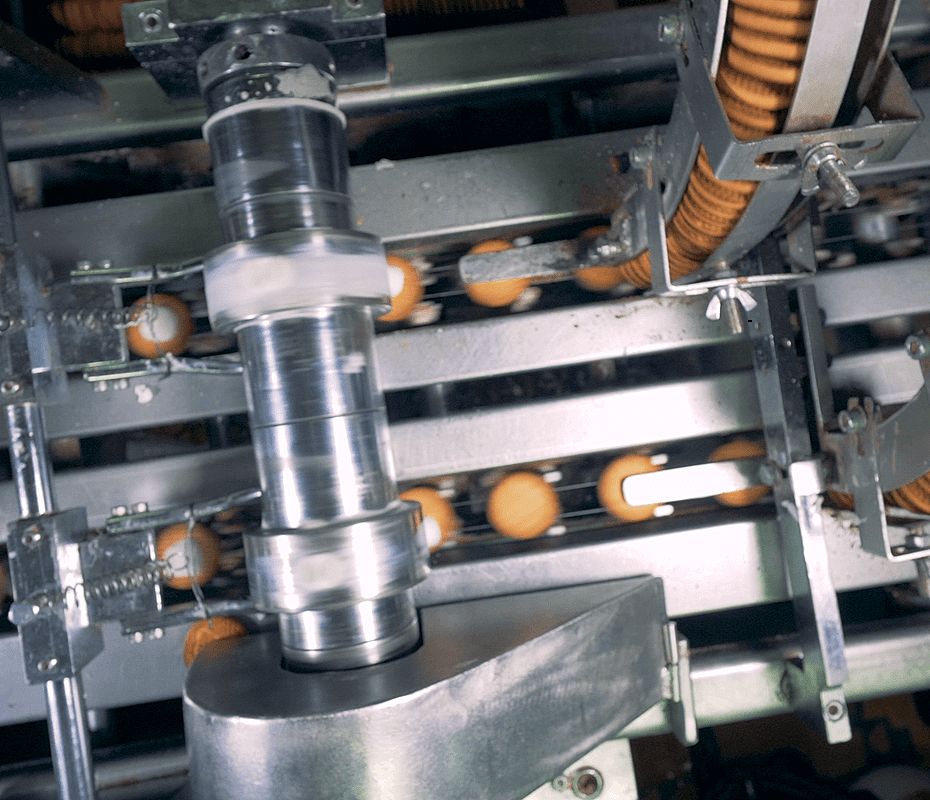
But many adversarial groups have also been creating ICS and SCADA-focused malware. TRITON, designated the “world’s most murderous malware” by MIT Technology Review, specifically attacks safety instrumented systems (SIS). A safety instrumented system takes “automated action to keep a plant in a safe state, or to put it into a safe state, when abnormal conditions are present;” SIS are the last line of defense in an industrial process, often preventing catastrophic disasters.
TRITON’s attacks against safety systems were a clarion call — moving beyond early attacks on production operations into the land of physical damage and potential life and safety calamities.
The logical progression is then to include more Internet of Things (IoT) and Industrial Internet of Things (IIoT) based modules. And experienced in the field performing cyber risk assessments and penetration tests, there are often online IT-based systems that are either inadvertently or purposefully linking an internet-connected system with the OT network. In cybersecurity parlance, this is known as a pivot point, allowing an attacker to pivot from successfully attacking an internet-enabled host to attacking the OT network, which isn’t supposed to have a direct connection to the internet.
Once a foothold is established in an OT-connected host, there is generally little protection left for an adversary to overcome. If the operation has visibility into their OT networks and can detect the intrusion, time is still required to isolate and remediate the adversarial actions. And that’s assuming the intrusion is detected immediately when the reality is adversaries often go months undetected within OT systems.
Apart from visibility and detection, few have protections in place to safeguard critical OT assets – like SIS. For example, if the programmable logic controller (PLC) and SIS readings were manipulated, would the operator know? Generally, the answer is no. (The SIS checks the PLCs, but nothing is validating the SIS.)
The ability to add various modules within malware allows an adversary to customize their attack to each unique environment. Is your HMI connected to a port on a VoIP phone that’s not sufficiently isolated? A module to attack that phone and use it as a pivot point onto the industrial control systems network could be employed.
Stepping up the OT cybersecurity: Protect critical assets
Every year, more and more vulnerabilities are discovered in OT equipment. And malicious actors are incorporating attacks against those ICS vulnerabilities into their suites. Those attacks will be used. And one needs to ask how prepared the operation is to notice, react to, and defend against those attacks? Can your operations (and bottom-line) survive the attempts?
It sounds like scenarios from the entertainment industry, but they’re real-world. The VoIP phone is an intentional example. During a cyber risk assessment within an industrial operation, the organization had a WIFI router in a conference room that was vulnerable to a Key Reinstallation Attack (KRACK). Once OT pen-testers got on the WIFI network exploiting that vulnerability, found a vulnerability within the VoIP telephone, executed a successful attack against that phone, bypassed a firewall, and gained a foothold on an OT network — within minutes and through a seemingly innocuous WIFI router in a conference room.
Modular malware allows an attacker to chain together environment-specific attacks and automate them to exploit very specific flaws. It can also more easily streamline adversarial toolsets or break reconnaissance and exploitation phases into better-delineated steps done by different teams.
The 2020 attack against Garmin is one example of the acceleration in IT/OT hybrid attacks, as the successful ransomware attack didn’t just stop the IT operations, but reportedly services and manufacturing. And it’s a reminder: just like safety, to prevent disasters, operations must take proactive steps to protect their operations, employees, and larger stakeholders.
Originally published February 25, 2021, updated February 25, 2021.