5 Min Read
The Cyber-attack on Garmin: Exposing GPS vulnerabilities
Written by Mission Secure
On July 23, Garmin’s millions of fitness-minded consumers worldwide found themselves unable to upload their latest exercise data. Garmin confirmed the outage, posting on its website and social media:
“We are currently experiencing an outage that affects Garmin.com and Garmin Connect. This outage also affects our call centers, and we are currently unable to receive any calls, emails or online chats. We are working to resolve the issue as quickly as possible and apologize for this inconvenience.”
While Garmin released few details, news of the latest high-profile cyber-attack quickly circulated media circuits. Garmin had fallen victim to the WastedLocker ransomware, a cyber-attack that encrypted its servers, leaving the organization dead in the water with a $10 million ransom. The suspected culprit behind the Garmin cyber-attack? EvilCorp, a Russian cybercrime group, believed to be the creators of WastedLocker.
After a five-day outage, Garmin’s suddenly announced services were being restored, and users were reassured their personal data was not stolen. Although consumer impact dominated the headlines, ZDNet notes EvilCorp is “one of the rare groups who don’t engage in this particular practice and has no history of stealing customer data before encrypting files.”
It is widely believed the company paid a ransom in exchange for the WastedLocker decryptor to recover its operations. BleepingComputer independently verified the ransomware and decryptor, stating:
“WastedLocker is an enterprise-targeting ransomware with no known weaknesses in their encryption algorithm. This lack of flaws means that a decryptor can not be made for free. To obtain a working decryption key, Garmin must have paid the ransom to the attackers.”
Broader Impacts with Cyber-physical Consequences
The media reports primarily focused on the Garmin cyber-attack in light of its impact on millions of consumer devices. However, Garmin is also the creator of numerous other GPS-based technologies. These include:
Aviation Systems: Navigation, radios, autopilots, active traffic systems, weather radar and receivers, ADS-B and transponders, flight instruments and indicators, engine information systems, displays, sensors, interfaces, and apps like flyGarmin.
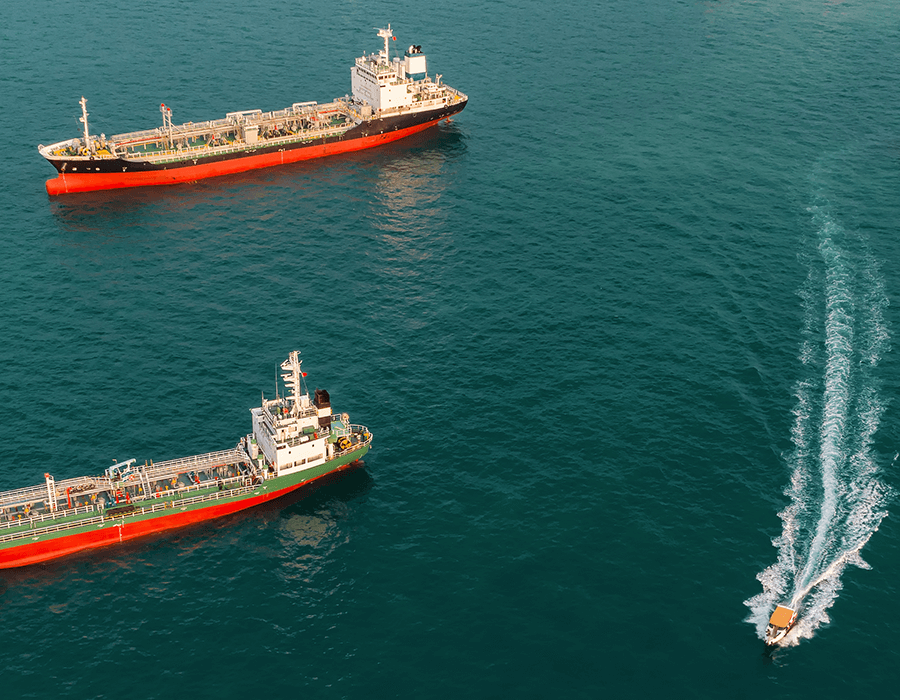
Maritime Systems: Autopilots, radars, chart plotters, Automatic Identification Systems (AIS), VHF radios, antennas and sensors, sonar black boxes, and the ActiveCaptain app, among others.
Automotive Systems: With direct-to-consumer and OEM solutions, Garmin also offers GPS-based technologies for vehicles and the automotive industry, including its Connected Cabin.
Navionics (GPS plotter charts), flyGarmin (aviation database app), and inReach (satellite communication with GPS) users also experienced outages. Some airplane pilots found themselves grounded, unable to download Garmin’s aviation database, “crucial for navigation and compliance with the FAA regulations.” Garmin Pilot was also down, further hindering flight schedules. In maritime, captains could not access the Navionics server, Navionics Boating app, Chart Installer, and Navionics Chart Viewer.
A Warning: Protecting GPS Against Cyber-attacks
“It’s been over a week since hackers crippled Garmin with a ransomware attack, and five days since its services started flickering back to life. The company still hasn’t fully recovered, as syncing issues and delays continue to haunt corners of the Garmin Connect platform. Two things, though, are clear: It could have been worse for Garmin. And it’s only a matter of time before ransomware’s big game hunters strike again.”
- Wired, The Garmin Hack Was a Warning
With far riskier and dangerous consequences, the Garmin attack serves as a warning, illuminating modern-day navigation systems’ fragility and our dependency on them. Various industries rely on GPS data for critical navigation, control system, and operational processes, including the maritime, aviation, automotive, and defense industries. And yet, these commercial GPS systems remain vulnerable to GPS jamming, spoofing, and, in Garmin’s case, cyber-attacks. What’s more—the Garmin attack illustrates that these operations come to a standstill without accurate GPS or navigational data.
Examples of GPS Cyber-attacks
GPS attacks have occurred across industries, including defense, maritime, and aviation. There are two main types of Global Navigation Satellite Systems (GNSS) or GPS cyber-attacks: GPS jamming and GPS spoofing.
GPS jamming results in users losing GPS location and related information. GPS jamming takes advantage of vulnerable lower power ultra-high-frequency radio signals over long distances (12,000 miles from satellites). An attacker can spin up a software-defined radio (via a laptop) and send out higher power broadcasts of distortion using the same GPS radio frequency. The GPS receiver locks on to this distorted signal and loses its correct position and timing. Without a land-based terrestrial backup signal, the GPS receiver device on an aircraft, vessel, traffic light, or phone cannot provide data (much less accurate data) required for valid control systems processes or simple navigational tasks.
GPS spoofing results in inaccurate location and related information fed to the end-user. GPS spoofing uses the same methodology as GPS jamming. An attacker provides a valid (slightly higher-powered) radio frequency signal with seemingly legitimate timing and control information to the GPS receiver. Then, the attacker carefully increases signal strength nominally to trick the receiver into staying locked onto the signal and trusting the position, navigation, and timing (PNT) information provided. GPS spoofing is a more sophisticated attack and not as easy to execute.
Over the past several years, Mission Secure has tracked an increasing array of GPS jamming and spoofing attacks. Below are a few examples to name a few:
In 2016, Iran captured two U.S. Navy command boats who strayed into Iranian waters. The sailors claimed their GPS showed they were in international waters.
The Black Sea GPS spoofing incident in June 2017 is well-publicized where over 20 vessels in the Black Sea region showed their locations many miles in-land.
In March 2019, the Center for Advanced Defense Studies (C4ADS) published a report on GPS spoofing incidents, noting “9,883 GNSS spoofing instances affecting 1,311 vessels across ten locations in Russia, Crimea, and Syria between February 2016 and November 2018.”
Earlier this year, the U.S. government received inquiries regarding GPS circle spoofing in Iran. Coincidentally, the Iranian GPS circle spoofing analysis highlights how Strava data also had anomalies for users. (Strava is a strategic Garmin partner and area of service outage with Garmin devices unable to upload to Strava.)
Vessel operations and industrial control systems rely on GPS as a critical input. Disruption or false information could negatively impact operations; a GPS-based attack combined with a cyber-attack on control systems could have a material and adverse impact.
Securing Critical GPS Systems
“But as hacking groups add both to their coffers and tool sets, it seems likely that Garmin is hardly an outlier—and only a matter of time before the next big target takes a big fall.”
- Wired, The Garmin Hack Was a Warning
Like other critical systems, organizations should take steps to secure their GPS systems from cyber-attacks. Below are a few measures to ensure the accuracy and integrity of GPS systems for maritime, aviation, and defense contexts.
Monitor and detect GPS discrepancies. GPS location data should be monitored and benchmarked against other navigational data, including validating and verifying PNT data required for safe and reliable operations. GPS cyber-attacks often go undetected until the vessel or plane has terrestrial bearings (e.g., going to port or landing). However, using proprietary algorithms and contextual data can detect a compromised GPS signal in real-time, avoiding a costly detour or late delivery. This approach also includes forensics for post-event analysis.
Remediate GPS inaccuracies. Operators can be alerted to GPS anomalies when they occur, allowing them to investigate and remediate the error before the vessel is drawn drastically off course or switch to alternative location data sources. Leveraging cybersecurity systems, operators can also configure navigation systems to change to a backup source if a GPS incident occurs (i.e., jamming, spoofing, or other anomalies.)
Establish an incident response plan. In addition to having a robust cybersecurity and incident response strategy, organizations can gain valuable intel by participating in a cyber response group. For example, Mission Secure is part of the Maritime Cyber Emergency Response Team (MCERT) in conjunction with Wartsila. This group offers companies incident response support and serves as an information-sharing venue with others in the industry, such as active GPS discrepancies.
OT Cybersecurity
“GPS is made up of three parts – receivers, satellites, and ground stations. Any one of these parts is vulnerable to an attack.”
Merely $200 can buy a low-cost GPS jamming device over the internet; $10,000 can buy a high-powered GPS jammer. These systems are highly mobile, relatively easy to use, accessible, and often have a range of 10 to over 70 miles. More notorious are the nation-state actors already attributed with GPS-based attacks such as Iran and Russia. As Fortune states, “For the global maritime shipping industry, spotty satellite navigation is a disaster waiting to happen.”
It is a long-overdue necessity for GPS systems to be secured to the same level as other critical operational and safety systems. Garmin should be the wake-up call to secure critical operations against today’s cyber threats.
Originally published August 31, 2020, updated December 2, 2020.