4 Min Read
Maritime Security Incidents: Disruptive Cyber-attack Cripples Port Facility
Written by Mission Secure

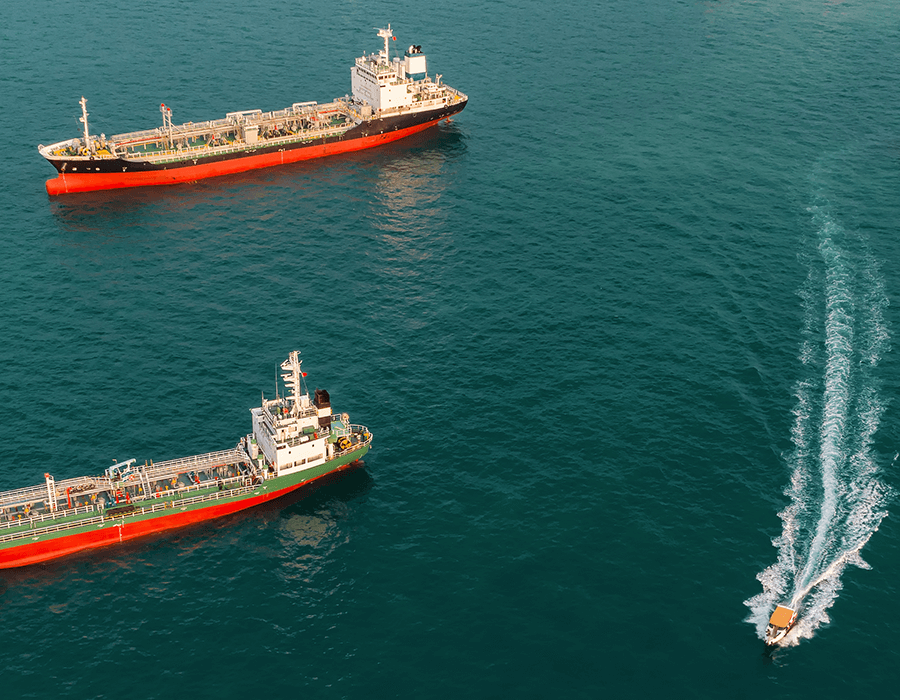
Geopolitical tensions are one of many maritime security challenges. It’s critical to have strong security measures in place across your vessel OT networks and between your interactions with port terminals.
On May 9, 2020, all shipping traffic at the Shahid Rajaee port terminal in Iran came to an abrupt halt. According to The Washington Post, an unknown foreign hacker briefly knocked the port’s computers offline, which led to massive backups on waterways and roads leading to the terminal.
Maritime networks have become an attractive playground for hackers, with cyber-attacks on vessel OT networks and systems increasing by 900% over the past three years. Attacks on vessel OT networks can be catastrophic, leading to injury, loss of life, asset damage or environmental impact.
In this post, we’ll walk through what happened at the Shahid Rajaee port terminal, why it happened, the aftermath, and how you can ensure your vessel OT networks are protected against debilitating cyberattacks.
Learn about specific protective security measures in our Comprehensive Guide to Maritime Cybersecurity.
What Happened?
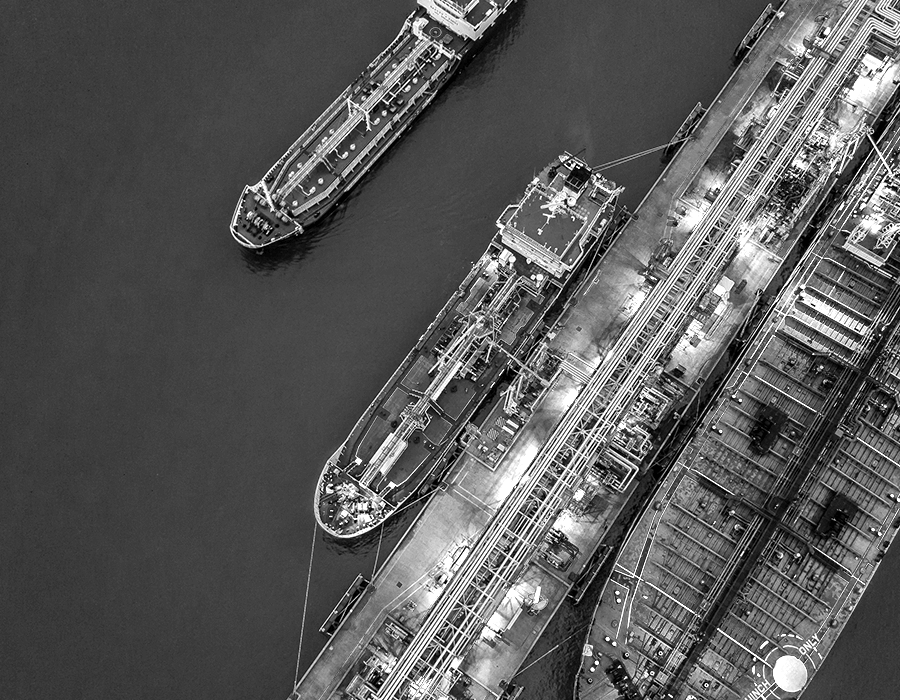
The Shahid Rajaee port facility is the newest of two major shipping terminals in the Iranian coastal city of Bandar Abbas, on the Strait of Hormuz. Computers that regulate the flow of vessels, trucks and goods at the port were knocked offline simultaneously on May 9, 2020, disrupting operations and causing road and waterway congestion that lasted several days.

According to an official, the damage was more severe than initially described by Iranian officials. Photos shown to The Washington Post dated May 9, 2020 exposed miles-long traffic jams on highways leading to the Shahid Rajaee port terminal. A photograph dated May 12, 2020 also showed dozens of loaded container ships in a waiting area off the coast.
The attack on the port’s computers was confirmed a day later by Mohammad Rastad, managing director of the Ports and Maritime Organization (PMO), who stated, “A recent cyberattack failed to penetrate the PMO’s systems and was only able to infiltrate and damage a number of private operating systems at the ports.”
Why Did This Happen?
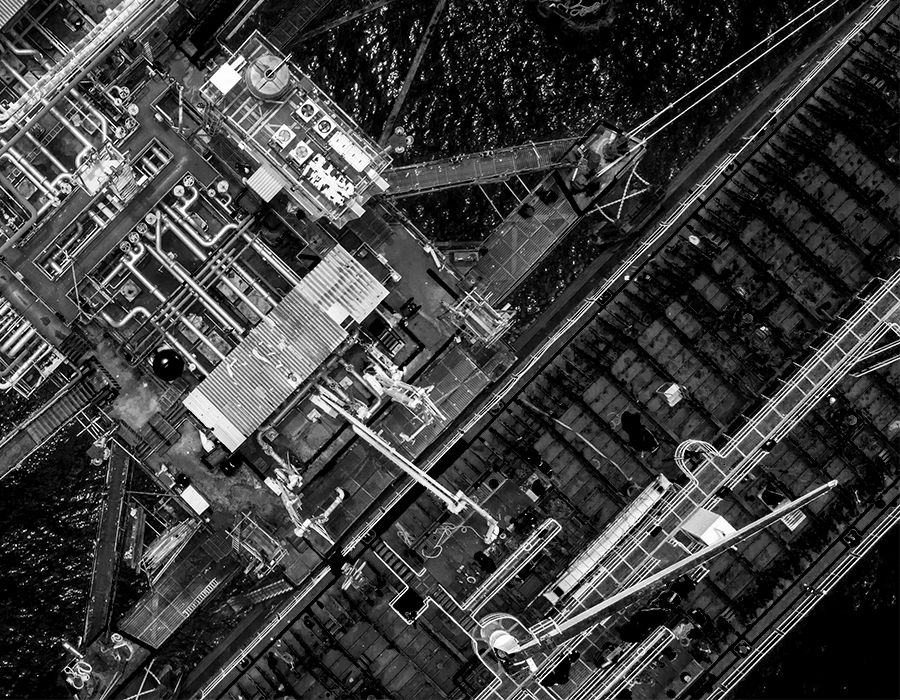
There has been some ongoing tension between Israel and Iran in the form of an alleged back and forth of attempted and successful cyberattacks against physical infrastructures. On April 24, 2020, an attempted cyberattack on Israeli water facilities (which Iran has denied any involvement) caused some temporary disruptions in some local water systems. The attempted attack, which targeted programmable logic controllers (PLCs) that operate valves for water distribution networks, was routed through computer servers in Europe and the United States. While PLCs tend to be attractive targets for hackers due to their lack of security, the incident was quickly detected and thwarted before it could cause significant damage.
Water facility cyber-attack: While the April attack on Israel’s water facilities was downplayed, Western intelligence sources believe that the hackers attempted to alter water chlorine levels before being detected and stopped. If the attack hadn’t been stopped and water chlorine levels had been adjusted, attackers could have caused mild poisoning of the local population served by the affected treatment facility.
There is speculation that the attack on Shahid Rajaee was retaliation by Israel and intended to send a warning to Iran without inflicting any significant physical harm or casualties. And while details are scarce on the actual execution of the cyberattack against the Shahid Rajaee port terminal, it is more than likely that the Terminal Operating System (TOS) that controls and manages the entire port was targeted through the various companies that have an interface to the TOS, given that only a number of private operating systems were damaged during the attack.
What’s the Aftermath?
There have been additional incidents that may be indicative of continued cyber warfare between the two nations:
Following the April 2020 attack, two more attacks hit Israel’s water management facilities in June 2020. One hit agricultural water pumps in upper Galilee, and the other hit water pumps in the central province of Mateh Yehuda. In a Water Authority statement, the affected facilities were specific, small drainage installations that were immediately repaired without any harm done.
There have also been several accidents and explosions at various facilities in Iran. On July 2, 2020, a fire that broke out at Iran’s Natanz Nuclear Facility is believed to be the result of a cyberattack, according to three Iranian officials. A spokesman for Iran’s Atomic Energy Organization stated that while the incident caused significant damage and could slow down the development and production of advanced centrifuges in the medium term, there were no casualties.
UPDATE: On October 16, 2020, it was reported that Iran’s Port Authority had been hit in a cyberattack, a day after Iranian officials vaguely confirmed that two governmental departments had been attacked. The attack targeted the Port Authority’s infrastructure to disrupt the flow of goods in and out of the country but failed to affect the process.
UPDATE: On December 1, 2020, a group of Iranian hackers accessed an unprotected industrial control system at an Israeli water facility. The hackers were able to access a human-machine interface (HMI) system directly connected to the internet without any cyber protection for a reclaimed water reservoir. The owner made changes to prevent access to the HMI system without authentication after the hackers posted a video about their exploit.
While neither nation is officially claiming responsibility for any of these incidents, there might be additional incidents as both countries have stated they will respond accordingly if a cyberattack is used against them. We will keep updating this page as more unfolds.
Bookmark this page for the latest updates to this developing situation
Economic Impacts: Ports & Shipping
Shipping and ports go hand-in-hand. Disruption to one creates a ripple effect for the other — this is a fact we've already seen first-hand with the current global pandemic and oil crash.
With the historically low oil prices, many companies and ports began to struggle with storage. Bloomberg writes, "From California to Gibraltar, tankers have piled up as suppliers deal with the largest glut the world has ever seen and ports have become congested." The lack of storage prolonged voyages with tankers having no place to go — and at port, they clogged up a well-worn system, causing knock-on consequences. While there are many factors at play, the interdependencies between ports and shipping are stark — as European oil tankers voyage around South Africa’s Cape of Good Hope solely to prolong their journeys.
From another perspective, Lloyd's of London looked at the estimated damage of a coordinated cyber-attack against ports. In their worst-case scenario, a coordinated cyber-attack on 15 Asian ports would cost $110 billion. Additionally, 92% of the estimated costs from the cyber-attack are uninsured.
The report also projected the interrelated costs with countries linked to each port. Asian countries would lose $26 billion, followed by Europe at $623 million, and North America at $266 million. Related industries would also take a hit, with aerospace losing $28.2 billion, manufacturing at a $23.6 billion loss, and retail losing $18.5 billion. (The report and estimates are pre-COVID 19 figures.)
OT cybersecurity isn't just a must-have for ships and vessels. Onshore operations, ports, and terminals must also secure and protect their operations.
Keep Cyberattacks at Bay from Your Vessel OT Network
Geopolitical tensions are one of many maritime security challenges. It’s critical to have strong security measures in place across your vessel OT networks and between your interactions with port terminals. With a global pandemic that continues to impact the global economy and expand the attack surface, port, ship and offshore staff must adapt their cybersecurity operations accordingly to ensure their endpoints, critical systems and components are updated and protected. Start your path to protection with our Comprehensive Guide to Maritime Cybersecurity.
Originally published August 5, 2020, updated December 14, 2020.