2 Min Read
Making Cyber Vigilance the New Modus Operandi
Written by Matt Malone

It’s easy to understand how the COVID-19 pandemic changed our personal and professional lives.
What’s not so easy to understand is how some unscrupulous people have taken advantage of others during this time when we’re typically encouraged to work together towards a common benefit. Some of those unscrupulous people are hackers.
Over the last weeks, hackers unleashed a wave of cyber attacks. Computer Weekly reported, “The cumulative volume of coronavirus-related email lures and other threats is the largest collection of attack types exploiting a single theme for years, possibly ever.” For example, hackers attacked hospitals in Europe using phishing emails with links hidden under the mask of COVID-19 as a way to unlawfully gain entry to those hospital networks and unleash malicious software. The good news is this malicious software was found early, which enabled remediation efforts to begin quickly. The bad news is malware can remain undetected for years.
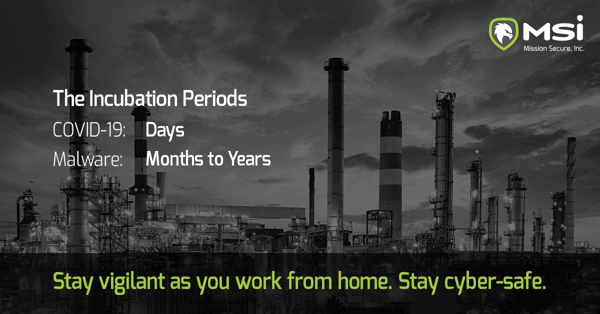
The incubation period of a virus, human or digital, lends insight into effective prevention and remediation actions. The mean human incubation time for COVID-19 in a person is just over five days, according to ScienceDaily; most people (97.5%) who develop symptoms will do so within 11.5 days of infection. These measures mean an infected person can carry and spread the virus for nearly two weeks before symptoms begin to show.
Malware and computer viruses also possess incubation periods. And during this unprecedented time of working from home and within an escalating cyber threat environment, these measures underscore the importance of remaining cyber vigilant.
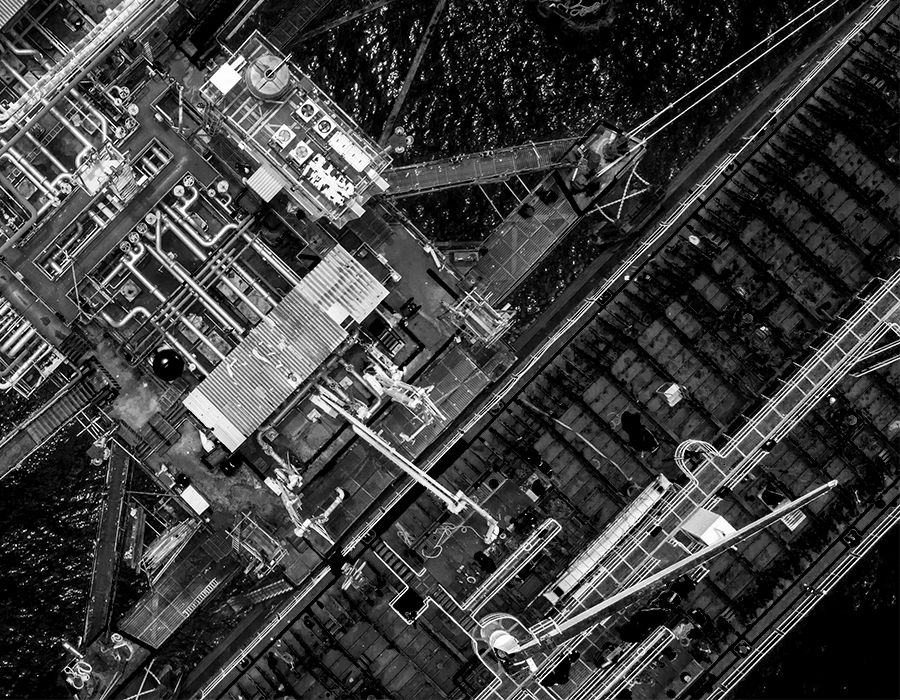
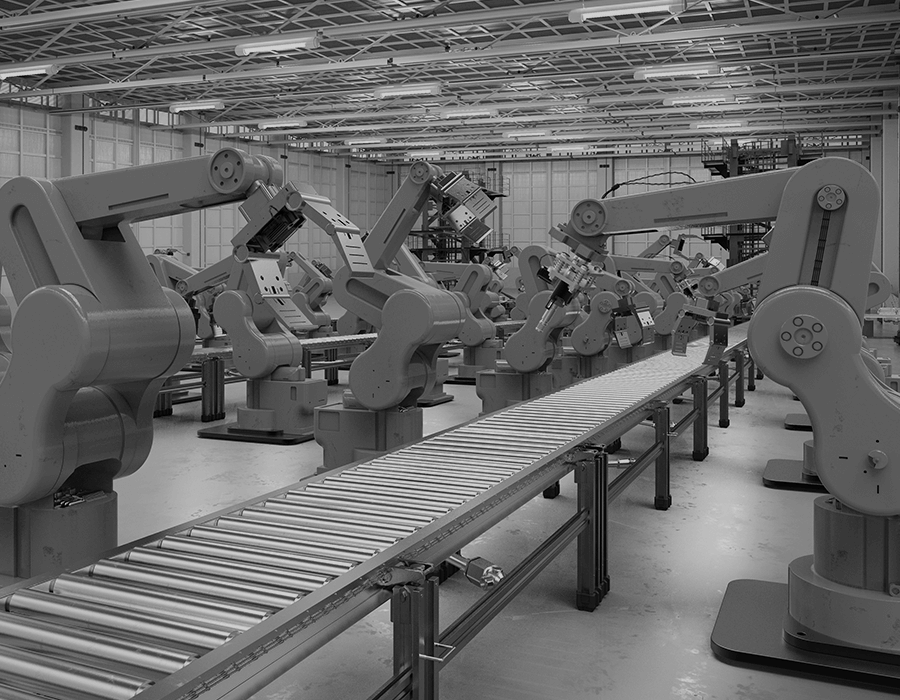
For industrial operations like energy, power, and manufacturing, the mean incubation period for operational technology (OT) or industrial control system (ICS) networks infected with a computer virus or other types of malware is notoriously long. Havex, for example, had an incubation period of at least three years. More recently, the malware attack at India’s Kundankulam Nuclear Power Plant (KKNPP) reportedly started in May 2019, first discovered in September of the same year or nearly four months later. The actual attack occurred at the end of October after a third-party reported it to the industrial operation.
Moreover, during this incubation period, the malicious software can perform discrete actions that are often unnoticed. Any “symptoms,” if you will, maybe mild and unnoticeable. And often, intelligence gathering and data collection are part of the end goal, as was the case with KKNPP, where the attack focused on collecting technical information. A minor increase in bandwidth here, a few gigs of unaccounted storage usage there. Before long, this can all add up to create a negative impact on your ICS network and operations.
While the current situation is temporary, the effects of poor cyber hygiene now could be felt months or years later. Long incubation periods, symptom-free or covert actions, and unknowing users can create a perfect environment for cyber attacks in industrial environments.
From phishing and mobile scams to VPN and application hacks, cyber attacks have drastically increased as the virtual and physical “office” expanding over the last several weeks. Technological innovation enabled us to adapt to the current situation; cybersecurity will ensure that our actions remain safe, secured, and beneficial. Just as everyone is encouraged to practice social distancing and good sanitization habits, we must also stay vigilant in our cyber hygiene practices.
As such, we’ve compiled a few resources to facilitate and remind individuals of cyber best practices when working from home.
National Cyber Security Alliance Resource Library: https://staysafeonline.org/covid-19-security-resource-library/
U.S. DHS’ CISA Tips: https://www.us-cert.gov/ncas/tips
Stay safe—at home and online.
Originally published April 7, 2020, updated November 19, 2020.