5 Min Read
Words of Wisdom from an Industrial Ethical Hacker
Written by Mission Secure
October is National Cybersecurity Awareness Month (NCSAM). The annual collaborative effort between government and industry aims to raise awareness about the importance of cybersecurity and ensure all have the resource to be safe and secure.
Led by the United States’ Cybersecurity and Infrastructure Security Agency (CISA) and the National Cyber Security Alliance (NCSA), this year’s theme—Do your part. #BeCyberSmart— encourages individuals and organizations to own their role in protecting their part of cyberspace, stressing personal accountability, and the importance of taking proactive steps to enhance cybersecurity. At Mission Secure, cybersecurity is what we do. In support of NCSAM 2020, we’ve put together short “Interview Bytes” to discuss cybersecurity from an operational technology (OT) and industrial control system (ICS) perspective.
Interview Bytes | Week 2: Securing Devices at Home and Work.
“It’s that chain of attack. It’s not necessarily one bad thing. It’s three bad things that lead to a terrible situation.”
The ramifications of an attack on Operational Technology (OT) or cyber-physical systems are far-reaching. According to a new Gartner report, by 2024, 75% of CEOs will be personally liable for cyber-physical security incidents. By 2023, a cyber-physical attack’s financial impact resulting in fatalities is expected to reach over $1 billion dollars. Gartner states, “Even without taking the actual value of a human life into the equation, the costs for organizations in terms of compensation, litigation, insurance, regulatory fines and reputation loss will be significant.”
Despite the heightened level of awareness, risks, and repercussions, there are few reported industrial cyber incidents. Stuxnet, TRITON, Havex, CrashOveride, NotPetya—the known examples of OT cyber-attacks are widely pointed to by practitioners and cybersecurity experts, but often seem more anecdotal than factual.
Even industries with more stringent cybersecurity regulations like bulk electric power have relatively limited reporting requirements. FERC and NERC CIP recently expanded their reporting requirements to include attempts at compromising systems, thereby lowering the reporting threshold to encompass a larger number of cyber incidents.
With a substantial increase in cyber-attacks throughout 2020, it is clear attacks are occurring—even if the victims, perpetrators, and impacts are not widely shared. This segment looks at industrial control systems and critical industries from a hacker’s point of view to illuminate the reality of today’s cyber threats.
Learn more as Weston Hecker, Cyber Evangelist and Ethical Hacker, shares his insights into industrial cyber threats and steps organizations can take to boost their cybersecurity.
Question: First, as an ethical hacker, what do you do?
From a Hacker’s Perspective | Weston Hecker, Cyber Evangelist and Ethical Hacker: It’s kind of a new testing in the industry. You know, five years ago people were pen-testing. But they weren’t they weren’t necessarily pen-testing some of the industrial control systems. Because, you know, we barely had enough engineers to fill the positions nonetheless, pen testers that understood how to break those same positions.
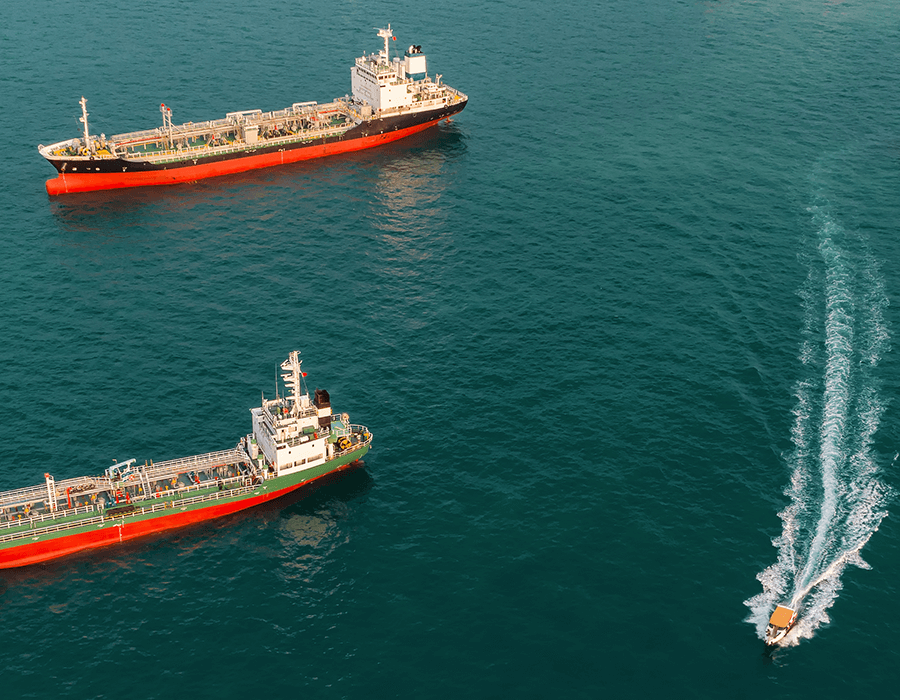
So, I’ve been doing pen-testing for 17 years. I focused on telecom for about three years, went to oil rigs, military vehicles, airplanes, trains, airports. I do a lot of the weird stuff that not a lot of other pen-testers do or what we call classical pen-testing.
Question: What advice do you have for companies looking to boost their cybersecurity?
From a Hacker’s Perspective | Weston Hecker, Cyber Evangelist and Ethical Hacker: Definitely, the first things they can do is finding out what is all on their network. Just know what’s on your network. Have a good inventory of what is collected. Make sure that your segmentation is up to snuff and following the best practices. And patch your systems. Keep track of what is actually out there for vulnerabilities for your systems. Something that happened six years ago is a huge example of it. I’ve used an attack from 2016 to literally get on probably 50% of my vessels that I’ve ended up doing full compromises. It’s something where if they would have just simply patched. It’s that chain of attack. It’s not necessarily one bad thing. It’s three bad things that lead to a terrible situation.
Securing Devices at Home and Work: Tip of the week
Weston’s recommendations for greater cybersecurity apply equally to both home and office environments, perhaps even more so in today’s remote working world. The first step is knowing what’s on your network so that you can protect it. Who is accessing what asset, at what time, and for what purpose?
Tip of the Week: Inventory, segment, and patch. It’s not one cyber mistake that leaves you vulnerable. It’s the chain of attack, or the three holes, that lead to a bad situation.
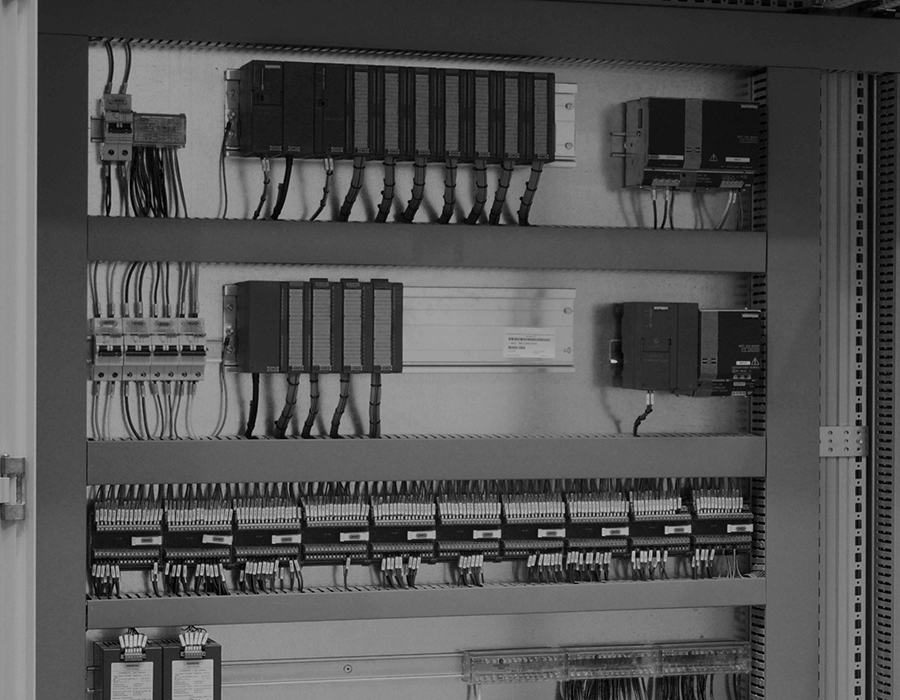
Next, network and device segmentation should be part of the defense in depth security approach for all critical industrial control system (ICS) environments. It is a physical security best practice learned over centuries, and an IT security best practice learned over the last several decades. Segmentation provides a much more robust security posture than a simple perimeter-only defense. With perimeter-only protection, once an adversary gains access, nothing prevents them from traversing the network unchallenged. Segmentation and micro-segmentation stop unhindered access in IT environments and should be doing the same in ICS environments.
In a work-from-home environment, segmentation still applies. For example, in a segmented or zero-trust environment, a third-party vendor has monitored and controlled access to specific areas of the network. Whether its employees working at home or vendors working from their offices, segmentation ensures only authorized activities are taking place and no unnecessary or unintentional threats are introduced into the operational environment.
In operational environments where 24/7 availability and uptime are crucial, patching vulnerabilities is often arduous. But unpatched assets leave operations exposed and vulnerable to attack—a fact we’ve seen in the headlines this year. But in establishing segmentation and implementing a zero-trust model of security, organizations can also ‘virtually’ patch their systems by monitoring and controlling access to each asset in real-time, further reducing risks and the likelihood of a cyber incident. Zero-trust in an ICS environment is a principle of maintaining strict access and communications controls by ensuring only securely authenticated users and devices have access to each process or device within the network. Even internal communications are not trusted by default.
OT environments have different equipment requirements than IT environments. These ICS environments require equipment designed to withstand harsh environments, which rules out your traditional IT equipment. But segmentation and a zero-trust model of security is definitely achievable, and here’s why industrial operations should segment—the OT way.
Do Your Part. #BeCyberSmart
As cyber adversaries become even more sophisticated in their tactics, cyber-attacks against OT environments are inevitably becoming the norm rather than exceptions. It’s time for organizations and individuals to take a look at every aspect of their critical operations to ensure they’re protected and resilient against these growing threats.
More from Weston on OT Cybersecurity:
Traffic Signal Systems: From a Hacker’s Perspective
Maritime Cyber Risk: From a Hacker’s Point of View
About the Speaker:
Weston Hecker contributes a wealth of cybersecurity expertise as a cyber evangelist and ethical hacker with over 17 years of pen-testing and 14 years of experience in cybersecurity research and programming. Weston’s found several software and firmware vulnerabilities, including Microsoft, Samsung, HTC, and Verizon. He works with organizations on their cybersecurity strategies, including leaders in oil and gas, chemicals, maritime, and defense sectors.
A regular on the cybersecurity circuit, Weston’s delivered over 50 presentations ranging from industry-leading events to regional conferences and universities. Notable events include Blackhat, Defcon, ISC2-Security Congress, SC-Congress, BSIDESBoston, and TakedownCON. Weston’s work with universities includes projects and training such as the “Hacking Oil Rigs for Profit” event at the University of Houston. He’s also working on a major university’s project with the Department of Homeland Security on 911 emergency systems and attack mitigation. Weston attended school in Minneapolis, where he studied Computer Science and Geophysics.
Originally published October 14, 2020, updated November 19, 2020.