5 Min Read
When Cybersecurity Regulation Becomes Mandatory
Written by Paul Robertson

Sunday, June 27th, marked the 30-day vulnerability assessment report deadline prescribed in late May by the Transportation Security Administration (TSA). In direct response to the Colonial Pipeline cyber-attack that shut down operations for a week and under a cloud of ongoing, increasingly bold, and sophisticated cyber-attacks, the U.S government has taken steps to make a concerted effort to bolster critical infrastructure cybersecurity.
Operations across critical infrastructure industries must address cybersecurity. But at the same time, sectors and practitioners are pondering what the future will look like for cybersecurity. What role will the government play? And will there be increased mandatory regulations?
Cyber threats for critical infrastructure: How did we get here?
Especially in the IT realm, cybersecurity isn’t new; it’s required to adopt efficiency-creating technologies while minimizing risks to the business. But when it comes to critical infrastructure, and especially in the industrial control system (ICS) or operational technology (OT) arenas, technology was adopted before security was an issue. Because, at that time, air-gapping was still widely used and effective – which is not the case today. In our assessments, we often find that customers are much more exposed and less air gaped than they believed themselves to be.
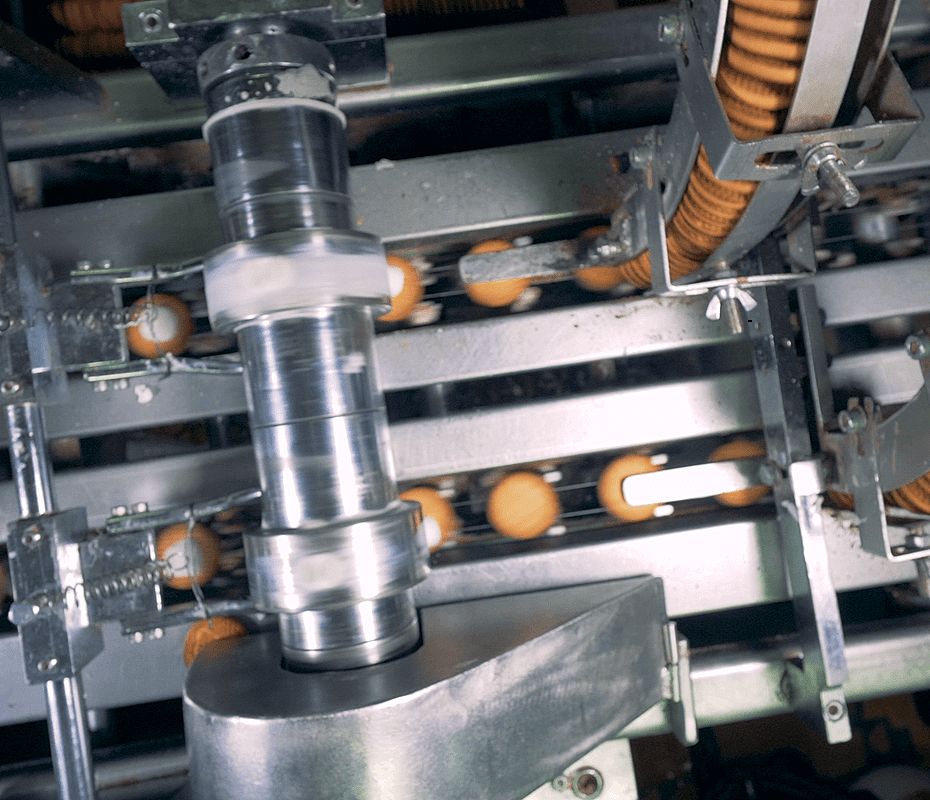
As critical infrastructure industries adopted new technologies, from IT to field sensors, they inadvertently converged and connected operational physical processes to the digital world. And in doing so, organizations became exposed to a host of new cyber threats that IT teams and operators were ill-prepared to combat.
In simplistic terms, that is what happened to Colonial Pipeline. An IT vulnerability became a full operation shut down out of an abundance of caution and to “contain the threat.” That is, once infiltrated, there was little control, protection, or confidence that the threat could be contained without shutting down the pipelines.
Colonial Pipeline, followed shortly by JBS Foods, highlighted in short succession the vulnerabilities in our ecosystems. Jointly paying $16 million in ransom (some of which was recovered), each attack’s costs exponentially grow when adding impacts to the supply chain, consumers, reputation, and rebuilding operations.
NERC CIP, NIST CSF, The NIS Directive: The role of regulation for cybersecurity
To date, many critical infrastructure industries are following guidelines and best practices to secure their operations – the unregulated group. The Pipeline Security Guidelines, for example, were published in 2018 and recently updated following the TSA directive (which included mandatory components). In manufacturing, CISA has published guides to bolster the industry’s cybersecurity, as is the case for most sectors. The foundation of these (as well as mandatory regulations) is often the NIST Cyber Security Framework (NIST CSF).
But a few have followed a more strict and mandatory approach or the regulated group. For example, the North American Electric Reliability Corporation Critical Infrastructure Protection plan (NERC CIP), administered by the Federal Energy Regulatory Commission (FERC), governs North America’s bulk electric system (BES) with mandatory regulations, audits, and fines. The largest NERC penalty currently on record is $10 million issued for 120 violations over four years.
Similarly, NEI 08-09 regulates cybersecurity for the nuclear energy industry. And abroad, the NIS Directive governs industries in Europe, including telecommunications.
As owners and operators of critical pipelines look to comply with the upcoming TSA deadline, the new directive begs the question: Is increased regulation up next for pipelines? And if so, is the TSA the body to administer it?
Power Magazine indicates the industry is seeking FERC’s experience and oversight for pipeline regulations, perhaps leading to a NERC CIP-style program beyond bulk power. But cybersecurity practitioners will hark that compliance does not equate to security – also a challenge bulk power has struggled with throughout the years. So, what should owners and operators do in the pipeline industry and beyond?
Here are three steps that nearly all frameworks (and regulations) suggest. Undertaking these will bolster your security posture and future compliance efforts should regulations be applied.
1. Do a proper, in-depth vulnerability assessment – and it should take longer than 30 days
TSA’s 30-day vulnerability assessment deadline is a good start. But it’s just a start and perhaps an indicator of a ‘knee-jerk’ reaction that critics have levied. The fact is, operations can uncover a lot in 30 days, but there is also a lot that they can miss.
Cyber adversaries are notorious for lying dormant in systems before attacking. Havex, for example, had an incubation period of at least three years. More recently, the malware attack at India’s Kundankulam Nuclear Power Plant (KKNPP) reportedly started in May 2019, first discovered in September of the same year or nearly four months later. The actual attack occurred at the end of October after a third party reported it to the industrial operation. A 30-day vulnerability assessment would miss both of those.
Operations need to conduct an in-depth assessment that covers what is and isn’t know. Piping and instrumentation (P&ID) diagrams are often out of date, so even walking the facility will uncover new assets and potential vulnerabilities. Assets, traffic, behaviors, people, and processes need to be reviewed for a thorough assessment. Once a proper lay of the land is done, organizations can understand how to protect their operations and make them resilient to cyber threats and attacks.
2. Segment your networks
“Ransomware continues to impact enterprises...Worms such as WannaCry and NotPetya rely on lateral movement to escalate a containable nuisance to a cataclysmic attack. Micro-segmentation and internal controls mitigate this problem and must be deployed as part of a Zero Trust strategy.”
- Forrester Research
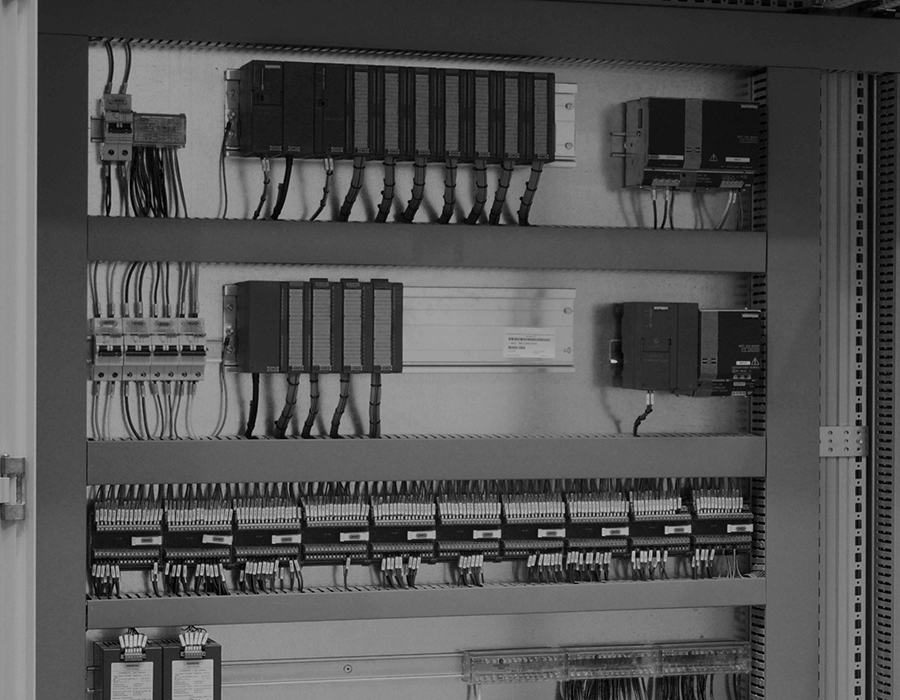
Network and device segmentation and micro-segmentation should be part of a Zero-Trust security approach for all critical industrial control system (ICS) environments. It is a physical security best practice learned over centuries and an IT security best practice deployed over the last several decades. Today, most critical infrastructure and industrial operations, like oil and gas, power, utilities, and manufacturing, already leverage simple segmentation between the corporate IT networks and the ICS or operational technology (OT) networks. But for most, that is where their segmentation stops.
Segmentation and micro-segmentation stop unhindered access in IT environments and should be doing the same in ICS network environments. It is invaluable for operations to leverage segmentation throughout the network and protect critical assets and processes. Network micro-segmentation increases the likelihood of cyber-attack detection and prevention by 300 – 1,000%, depending on the size of the network and tiers of micro-segmentation.
3. Apply a Zero-Trust approach to security
Over the last decade, threat intelligence and IDS solutions have expanded their capabilities to visualize devices with greater detail and uncover vulnerabilities in real-time. Yet, we continue to see growth in successful cyber-attacks targeting critical infrastructure. Critical infrastructure industries must move beyond the conservative threat intelligence and device visibility capabilities common in the market today to include real protection, automation, and resiliency functions. These functions are undeniably what is required to meet modern security needs, and for this, a Zero Trust Networking Access (ZTNA) approach is foundational.
A Zero-Trust model requires the adoption of a least privilege access strategy that assigns access permissions to users, applications, and data based on specific and defined needs. Secure access is enforced regardless of where (e.g., inside or outside the LAN) access is requested, and access controls are fine-grained and revocable. It is also important that all access control activity is logged and audited with the ability to generate alerts automatically.
Preparing for the future of cybersecurity
The future for critical infrastructure cybersecurity is likely to be a mix of mandatory regulations and voluntary frameworks. The government will continue to pay attention to cybersecurity until the threat and risk are reduced; if companies had protection today, not just visibility, it would likely be a different conversation.
Regardless, recent events and reactions spotlight a dire hole in our infrastructure, ecosystem, and supply chains – cybersecurity. Taking steps today to mitigate risk and bolster protection measures will strengthen operations in the short term, and better prepare them for any compliance requirements introduced in the future. So, take a thorough assessment of your current risk profile, and put in robust measures to protect your operations with cyber-resilience as the end goal.
Originally published June 29, 2021, updated June 29, 2021.