1 Min Read
Mission Secure Cyber Roundup | July 2021
Written by Mission Secure News Desk

Cybersecurity in the News
Recent high-profile cyber-attacks on critical infrastructure spark a regulatory response from the U.S. government. Deadline passes for pipeline owners and operators to submit vulnerability assessment reports to the Transportation Security Administration (TSA). Cyber vulnerabilities reported for FATEK WinProladder and Mitsubishi Electric's Human-Machine-Interfaces (HMIs). Fake "DarkSide" groups target the energy and food industries. VMWare Carbon Black patch is available; patch now if you have assets.
Spotlight
When Cybersecurity Regulation Becomes Mandatory
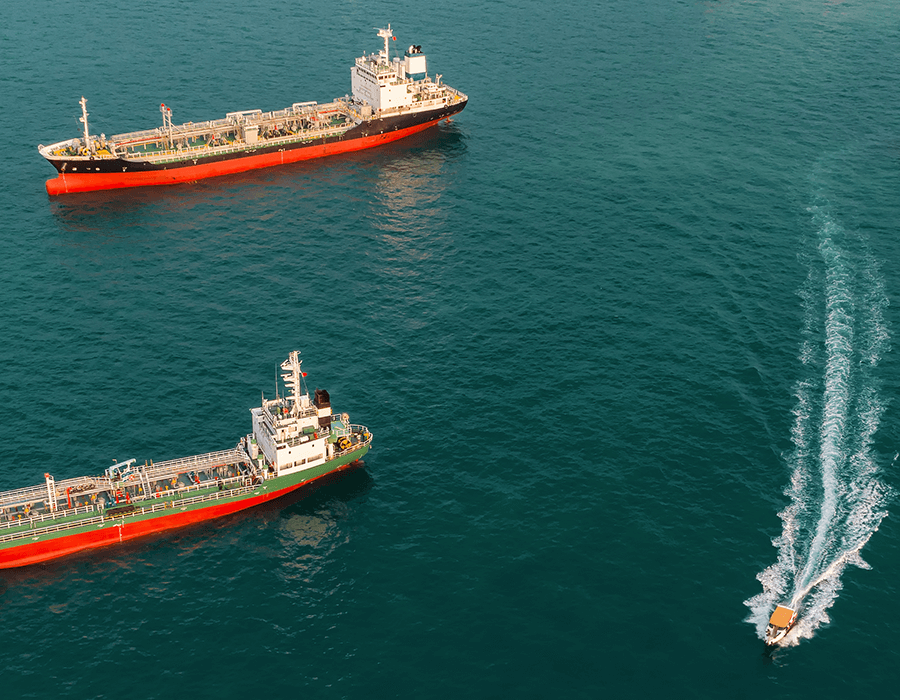
Sunday, June 27th, marked the 30-day vulnerability assessment report deadline prescribed in late May by the Transportation Security Administration (TSA). In direct response to the Colonial Pipeline cyber-attack that shut down operations for a week and under a cloud of ongoing, increasingly bold, and sophisticated cyber-attacks, the U.S government has taken steps to make a concerted effort to bolster critical infrastructure cybersecurity.
Operations across critical infrastructure industries must address cybersecurity. But at the same time, sectors and practitioners are pondering what the future will look like for cybersecurity. What role will the government play? And will there be increased mandatory regulations? Read More.
Cybersecurity News

New Vulnerability in the FATEK WinProladder
Used to design and deploy PLC ladder logic, FATEK WinProladder is vulnerable to out-of-bounds read. Read More >>>
Fake "DarkSide" Groups Proliferate
Several unknown actors using the now-defunct "DarkSide" name are targeting the energy and food industries. Read More >>>

Patch Available for VMWare Carbon Black
This is an important patch as it applies to the framework on which servers and machines are hosted. It's time to patch. Read More >>>

HMIs Vulnerable to Remote Code Executions
Several of Mitsubishi Electric's Human-Machine-Interfaces (HMIs) are vulnerable to remote code execution. Read More >>>
Get the latest news on the Mission Secure Blog!
Read more
Originally published June 29, 2021, updated June 29, 2021.